Researchers at Cyble Research and Intelligence Labs (CRIL) have uncovered an ongoing quishing campaign dubbed “Scanception,” which exploits QR code-based delivery mechanisms to distribute credential-harvesting URLs.
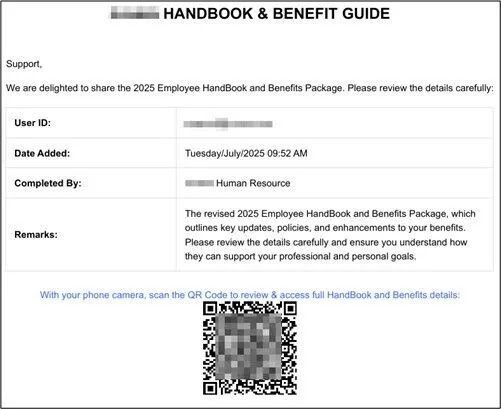
This advanced phishing operation begins with targeted emails containing PDF lures that mimic legitimate enterprise communications, urging recipients to scan embedded QR codes.
By shifting the attack surface to unmanaged personal mobile devices, the campaign effectively bypasses email gateways, endpoint detection and response (EDR) systems, and other perimeter defenses.
Over the past three months, CRIL has identified more than 600 unique phishing PDFs and associated emails, with nearly 80% evading detection on VirusTotal at the time of analysis.
Sophisticated Quishing Campaign
The lures are highly sophisticated, employing social engineering tactics that replicate HR workflows, financial approvals, and other business processes to build trust and increase user interaction rates.
This precision targeting spans multiple sectors, including technology, healthcare, manufacturing, and banking, financial services, and insurance (BFSI), with a global reach across North America, Europe, the Middle East, Africa (EMEA), and Asia-Pacific (APAC) regions.
The campaign’s evolution includes multi-page PDFs designed to evade static analysis engines that typically scan only initial pages, further complicating detection by antivirus and sandboxing tools.
At the core of Scanception’s technical sophistication is its abuse of trusted services and open redirectors to mask malicious infrastructure.
Attackers leverage platforms like YouTube, Google, Bing, Cisco, and Medium to relay victims through seemingly legitimate URLs, exploiting implicit trust in these domains to circumvent reputation-based filters and web proxies.
Adversary-in-the-Middle Tactics
For instance, encoded redirects append victim-specific parameters, such as base64-encoded email addresses, to personalize and track phishing attempts.
Upon scanning the QR code, users are directed to adversary-in-the-middle (AITM) phishing pages that impersonate services like Microsoft Office 365, complete with evasion mechanisms to detect automation tools such as Selenium, PhantomJS, or Burp Suite.
These pages disable right-click functionality, monitor for debugging every 100 milliseconds, and redirect to benign sites upon detection, thwarting forensic analysis.
The credential-harvesting process is multi-staged, involving browser fingerprinting to collect device metadata, followed by real-time exfiltration of credentials via POST requests to randomized endpoints generated using libraries like randexp.js.
This setup maintains an open channel with attacker-controlled servers, enabling the relay of multi-factor authentication (MFA) challenges such as OTPs or email verification codes in real time, facilitating session hijacking and account takeover.
Post-exploitation, victims are redirected to legitimate websites to minimize suspicion, allowing the campaign to persist undetected.
The operational scope of Scanception reveals a high-volume, tailored threat landscape, with similarities to tactics documented in prior research on QR code phishing and phishing-as-a-service (PhaaS) platforms.
Active across over 50 countries and impacting more than 70 sectors, the campaign demonstrates adaptive TTPs, including lure variations from single-page to multi-page decoys.
This convergence of social engineering, infrastructure abuse, and AITM techniques highlights a shift toward exploiting human vigilance and mobile endpoints beyond organizational control.
As the campaign remains active and evolving, security teams are urged to enhance awareness training, implement mobile device management (MDM) for personal devices, and monitor for anomalous redirects from trusted domains to mitigate these credential-theft risks.
Get Free Ultimate SOC Requirements Checklist Before you build, buy, or switch your SOC for 2025 - Download Now