Salt Typhoon represents one of the most persistent and sophisticated cyber threats targeting global critical infrastructure today. Believed to be linked to state-sponsored actors from the People’s Republic of China, this advanced persistent threat group has executed a series of high-impact campaigns against telecommunications providers, energy networks, and government systems—most notably across the United States.
Active since at least 2019, the group—also tracked as Earth Estries, GhostEmperor, and UNC2286—has demonstrated advanced capabilities in exploiting edge devices, maintaining deep persistence, and exfiltrating sensitive data across more than 80 countries.
While much of the public reporting has focused on U.S. targets, Salt Typhoon’s operations have extended into Europe, the Middle East, and Africa where it has targeted telecoms, government entities, and technology firms.
Its use of custom malware and exploitation of high-impact vulnerabilities in products from vendors like Ivanti, Fortinet, and Cisco underscores the strategic nature of its campaigns, which blend intelligence collection with geopolitical influence.
Leveraging zero-day exploits, obfuscation techniques, and lateral movement strategies, Salt Typhoon has demonstrated an alarming ability to evade detection and maintain long-term access to sensitive environments.
The group’s operations have exposed lawful intercept systems, compromised metadata for millions of users, and disrupted essential services, prompting coordinated responses from intelligence agencies and private-sector partners worldwide.
Darktrace recently observed activity in a European telecommunications organization consistent with Salt Typhoon’s known tactics, techniques and procedures, including dynamic-link library sideloading and abuse of legitimate software for stealth and execution.
The intrusion likely began with exploitation of a Citrix NetScaler Gateway appliance in the first week of July 2025. From there, the actor pivoted to Citrix Virtual Delivery Agent hosts in the client’s Machine Creation Services subnet.
Initial access activities in the intrusion originated from an endpoint potentially associated with the SoftEther VPN service, suggesting infrastructure obfuscation from the outset.
Darktrace subsequently observed the threat actor delivering a backdoor assessed with high confidence to be SNAPPYBEE, also known as Deed RAT, to multiple Citrix VDA hosts.
The backdoor was delivered to these internal endpoints as a DLL alongside legitimate executable files for antivirus software such as Norton Antivirus, Bkav Antivirus, and IObit Malware Fighter. This pattern of activity indicates that the attacker relied on DLL sideloading via legitimate antivirus software to execute their payloads.
Salt Typhoon and similar groups have a history of employing this technique, enabling them to execute payloads under the guise of trusted software and bypassing traditional security controls.
The backdoor delivered by the threat actor leveraged LightNode VPS endpoints for command-and-control, communicating over both HTTP and an unidentified TCP-based protocol. This dual-channel setup is consistent with Salt Typhoon known use of non-standard and layered protocols to evade detection.
Detection and Response Efforts
The HTTP communications displayed by the backdoor included POST requests with an Internet Explorer User-Agent header and Target URI patterns such as “/17ABE7F017ABE7F0”. One of the C2 hosts contacted by compromised endpoints was aar.gandhibludtric[.]com, a domain recently linked to Salt Typhoon.
Darktrace produced high-confidence detections in response to the early stages of the intrusion, with both the initial tooling and C2 activities being strongly covered by investigations by Darktrace Cyber AI Analyst investigations and Darktrace models.
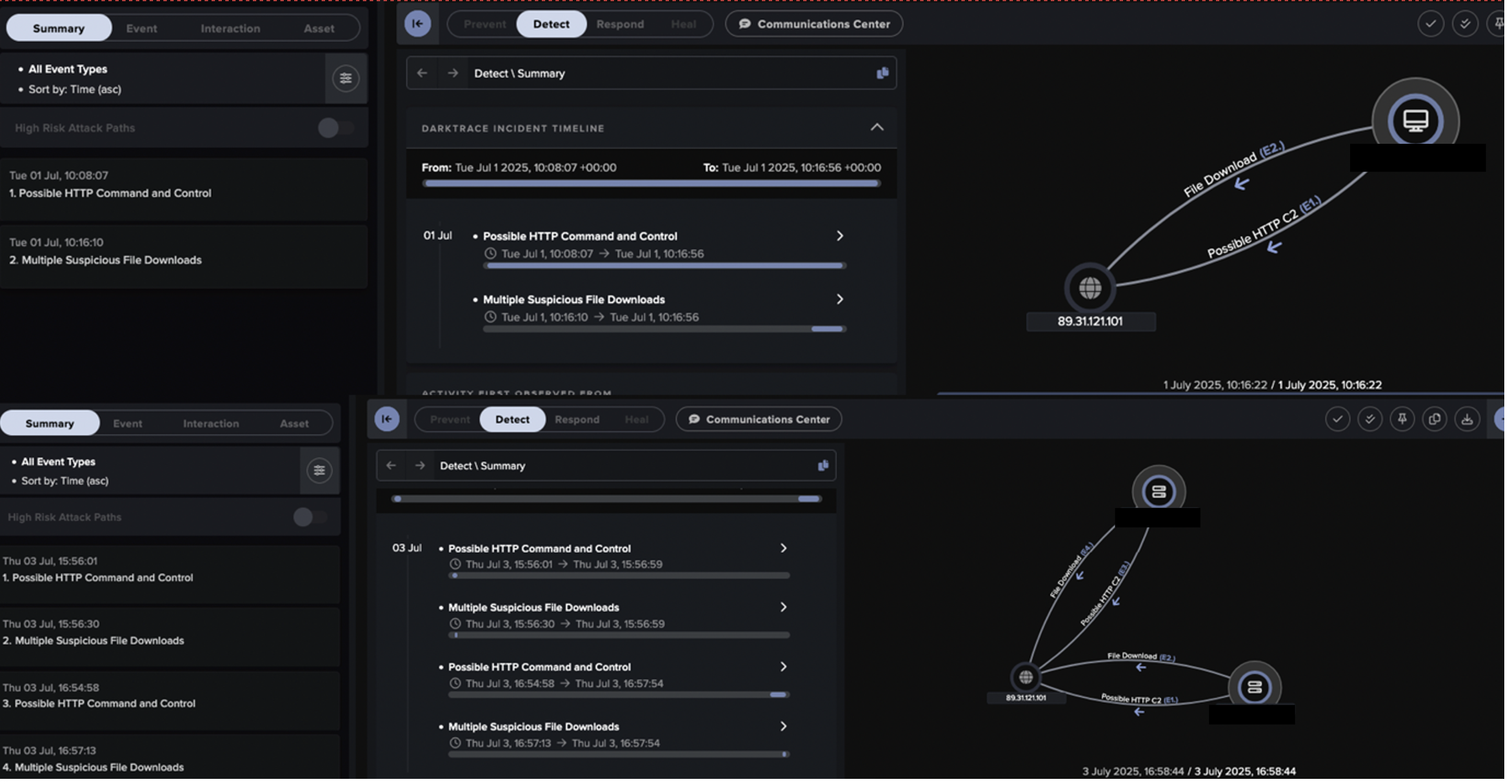
Despite the sophistication of the threat actor, the intrusion activity was identified and remediated before escalating beyond these early stages of the attack, with Darktrace’s timely high-confidence detections likely playing a key role in neutralizing the threat.
Darktrace’s Cyber AI Analyst autonomously investigated the model alerts generated during the early stages of the intrusion, discovering the initial tooling and C2 events and piecing them together into unified incidents representing the attacker’s progression.
Based on overlaps in tactics, techniques and procedures, staging patterns, infrastructure, and malware, Darktrace assesses with moderate confidence that the observed activity was consistent with Salt Typhoon.
As organizations reassess their threat models, Salt Typhoon serves as a stark reminder of the evolving nature of nation-state cyber operations and the urgent need for proactive defense strategies that rely on behavioral anomaly detection rather than signature-based approaches alone.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.