Shipping companies and medical laboratories in Asia have been the subject of a suspected espionage campaign carried out by a never-before-seen threat actor dubbed Hydrochasma.
The activity, which has been ongoing since October 2022, “relies exclusively on publicly available and living-off-the-land tools,” Symantec, by Broadcom Software, said in a report shared with The Hacker News.
There is no evidence available as yet to determine its origin or affiliation with known threat actors, but the cybersecurity company said the group may be having an interest in industry verticals that are involved in COVID-19-related treatments or vaccines.
The standout aspects of the campaign is the absence of data exfiltration and custom malware, with the threat actor employing open source tools for intelligence gathering. By using already available tools, the goal, it appears, is to not only confuse attribution efforts, but also to make the attacks stealthier.
The start of the infection chain is most likely a phishing message containing a resume-themed lure document that, when launched, grants initial access to the machine.
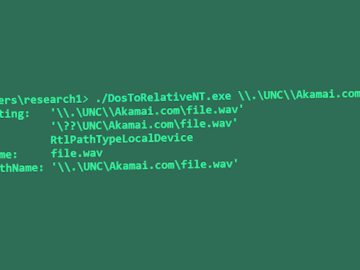
From there, the attackers have been observed deploying a trove of tools like Fast Reverse Proxy (FRP), Meterpreter, Cobalt Strike Beacon, Fscan, BrowserGhost, and Gost proxy.
“The tools deployed by Hydrochasma indicate a desire to achieve persistent and stealthy access to victim machines, as well as an effort to escalate privileges and spread laterally across victim networks,” the researchers said.
The abuse of FRP by hacking groups is well-documented. In October 2021, Positive Technologies disclosed attacks mounted by ChamelGang that involved using the tool to control compromised hosts.
Then last September, AhnLab Security Emergency response Center (ASEC) uncovered attacks targeting South Korean companies that leveraged FRP to establish remote access from already compromised servers in order to conceal the adversary’s origins.
Hydrochasma is not the only threat actor in recent months to completely eschew bespoke malware. This includes a cybercrime group dubbed OPERA1ER (aka Bluebottle) that makes extensive use of living-off-the-land, dual use tools and commodity malware in intrusions aimed at Francophone countries in Africa.