Cybercriminals are promoting a new phishing kit named ‘V3B’ on Telegram, which currently targets customers of 54 major financial institutes in Ireland, the Netherlands, Finland, Austria, Germany, France, Belgium, Greece, Luxembourg, and Italy.
The phishing kit, priced between $130-$450 per month depending on what is purchased, features advanced obfuscation, localization options, OTP/TAN/2FA support, live chat with victims, and various evasion mechanisms.
According to Resecurity researchers who discovered V3B, its Telegram channel already counts over 1,250 members, indicating the new phishing-as-a-service (PhaaS) platform is quickly gaining traction in the cybercrime space.
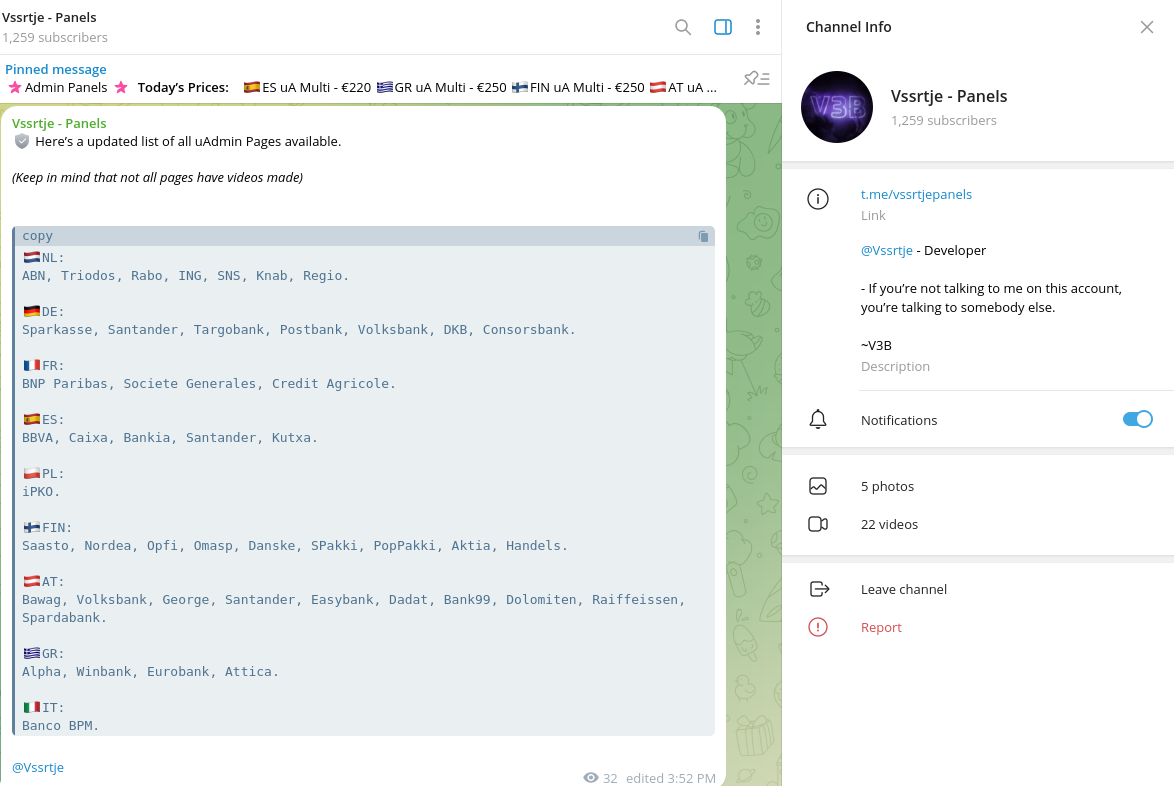
Source: Resecurity
V3B features
V3B uses heavily obfuscated JavaScript code on top of a custom CMS to evade detection by anti-phishing and search engine bots and protect from researchers.
It includes professionally translated pages in multiple languages like Finnish, French, Italian, Polish, and German to enhance the effectiveness of the phishing attacks, allowing threat actors to run multi-country campaigns.
The kit, which is designed to work on both mobile and desktop platforms, can intercept banking account credentials and information, as well as credit card details.
Additionally, the admin panel (uPanel) allows fraudsters to interact with victims in real time via a chat system to obtain one-time passwords (OTPs) by sending custom notifications.
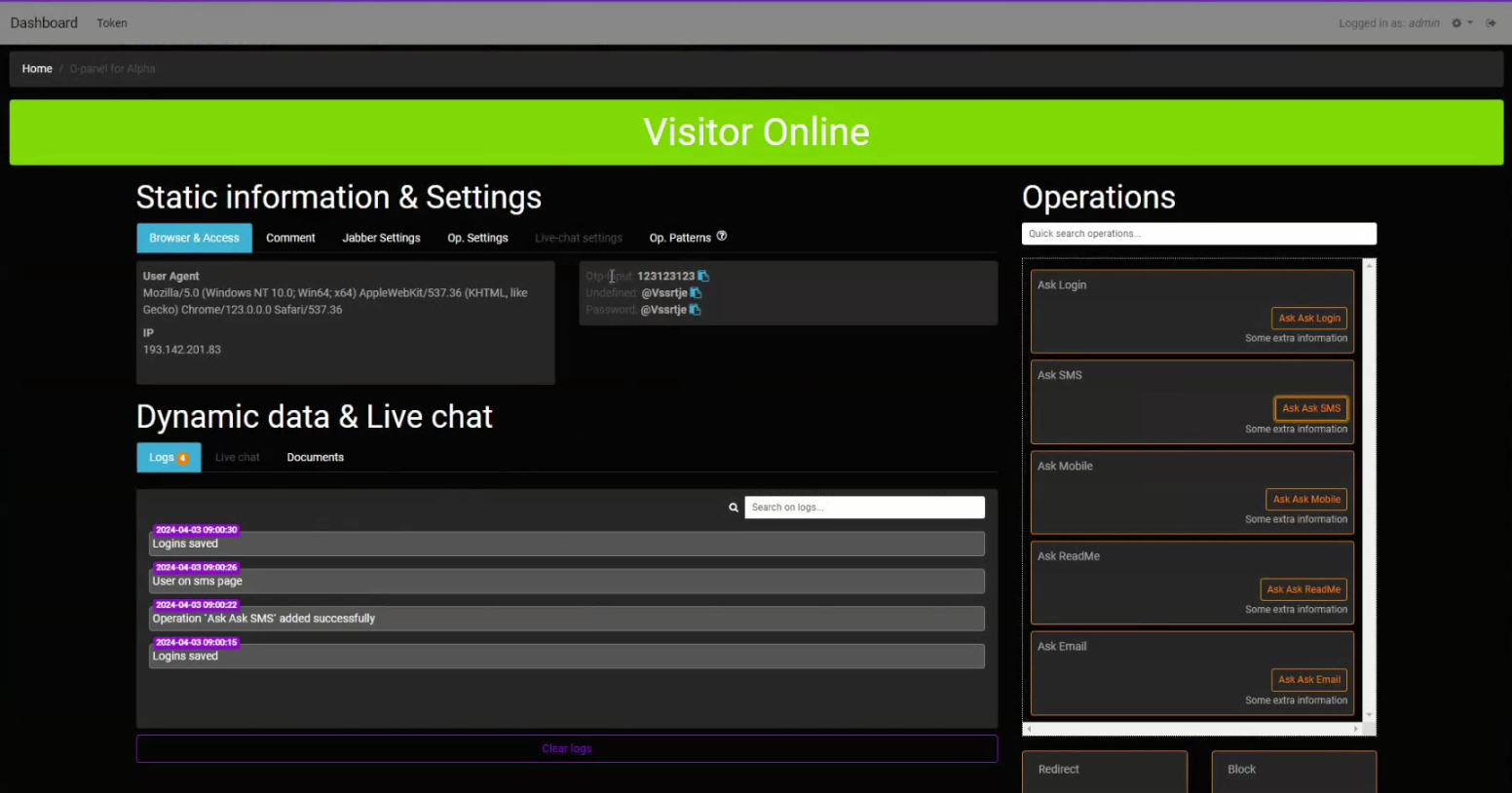
Source: Resecurity
Stolen information is transmitted back to the cybercriminals through the Telegram API.
Among the real-time interaction trigger options, there is a QR code login jacking feature that enables cybercriminals to generate QR codes for phishing pages, taking advantage of a false sense of legitimacy stemming from the victim’s familiarity with trusted services using that method.
Another notable feature of the V3B kit is support for PhotoTAN and Smart ID to bypass advanced authentication technologies that German and Swiss banks widely use.
“Technologies used for customer authentication by banks may vary,” explains Resecurity.
“However, the fact that fraudsters have started to implement support of alternative OTP/TAN validation mechanisms, rather than relying solely on traditional SMS-based methods, may confirm the challenges that fraud prevention teams will face in combating account takeover for both private and corporate customers.”
Phishing kits are key enablers of cybercrime, allowing low-skilled threat actors to launch highly damaging attacks against unsuspecting bank customers.
One of the largest PhaaS operations out there, LabHost, which targeted mainly U.S. and Canadian banks, was recently taken down by law enforcement authorities.
Thirty-seven people, including the original developer, were arrested in the law enforcement operation.
At the time of its bust, LabHost had 10,000 users worldwide, launching phishing attacks through 40,000 domains.
