A new “mass-spreading” social engineering campaign is targeting users of the Zimbra Collaboration email server with an aim to collect their login credentials for use in follow-on operations.
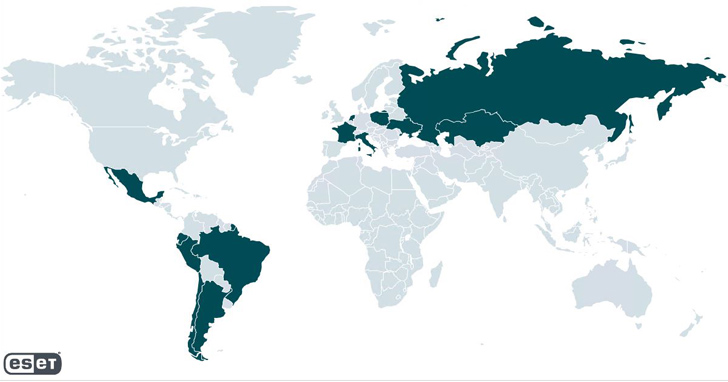
The activity, active since April 2023 and still ongoing, targets a wide range of small and medium businesses and governmental entities, most of which are located in Poland, Ecuador, Mexico, Italy, and Russia. It has not been attributed to any known threat actor or group.
“Initially, the target receives an email with a phishing page in the attached HTML file,” ESET researcher Viktor Šperka said in a report. “The email warns the target about an email server update, account deactivation, or similar issue and directs the user to click on the attached file.”

The messages also spoof the from address to appear as if they are coming from a Zimbra administrator in a likely attempt to convince the recipients into opening the attachment.
The HTML file contains a Zimbra login page tailored to the targeted organization, with the Username field prefilled with the victim’s email address to make it seem more authentic. Once the credentials are entered, they are collected from the HTML form and sent via a HTTPS POST request to an actor-controlled server.
What makes the attacks stand out is their ability to propagate further. Subsequent phishing waves have leveraged accounts of previously targeted, legitimate companies, suggesting that the infiltrated administrator accounts associated with those victims were used to send emails to other entities of interest.

“One explanation is that the adversary relies on password reuse by the administrator targeted through phishing – i.e., using the same credentials for both email and administration,” Šperka noted.
While the campaign is not technically sophisticated, it banks on the fact that “HTML attachments contain legitimate code, and the only telltale element is a link pointing to the malicious host” that’s embedded in the source code.
“This way, it is much easier to circumvent reputation-based anti-spam policies, compared to phishing techniques where a malicious link is directly placed in the email body,” Šperka said.