Hackers are utilizing a new trick of using zero-point fonts in emails to make malicious emails appear as safely scanned by security tools in Microsoft Outlook.
Although the ZeroFont phishing technique has been used in the past, this is the first time it has been documented as used in this way.
In a new report by ISC Sans analyst Jan Kopriva, the researcher warns that this trick could make a massive difference in the effectiveness of phishing operations, and users should be aware of its existence and use in the wild.
ZeroFont attacks
The ZeroFont attack method, first documented by Avanan in 2018, is a phishing technique that exploits flaws in how AI and natural language processing (NLP) systems in email security platforms analyze text.
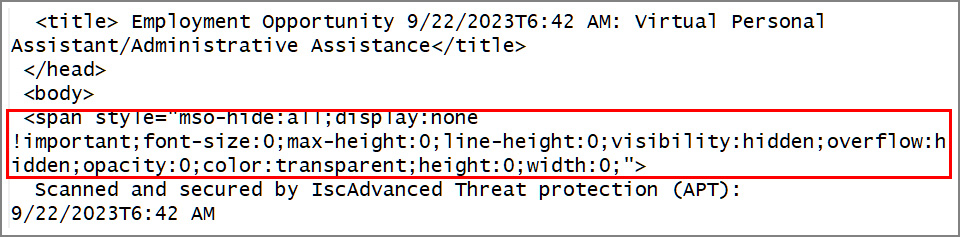
It involves inserting hidden words or characters in emails by setting the font size to zero, rendering the text invisible to human targets, yet keeping it readable by NLP algorithms.
This attack aims to evade security filters by inserting invisible benign terms that mix with suspicious visible content, skewing AI’s interpretation of the content and the result of security checks.
In its 2018 report, Avanan warned that ZeroFont bypassed Microsoft’s Office 365 Advanced Threat Protection (ATP) even when the emails contained known malicious keywords.
Hiding bogus antivirus scans
In a new phishing email seen by Kopriva, a threat actor uses the ZeroFont attack to manipulate message previews on widely used email clients such as Microsoft Outlook.
Specifically, the email in question displayed a different message in Outlook’s email list than in the preview pane.
As you can see below, the email listing pane reads “Scanned and secured by Isc®Advanced Threat protection (APT): 9/22/2023T6:42 AM,” whereas the beginning of the email in the preview/reading pane displays “Job Offer | Employment Opportunity.”
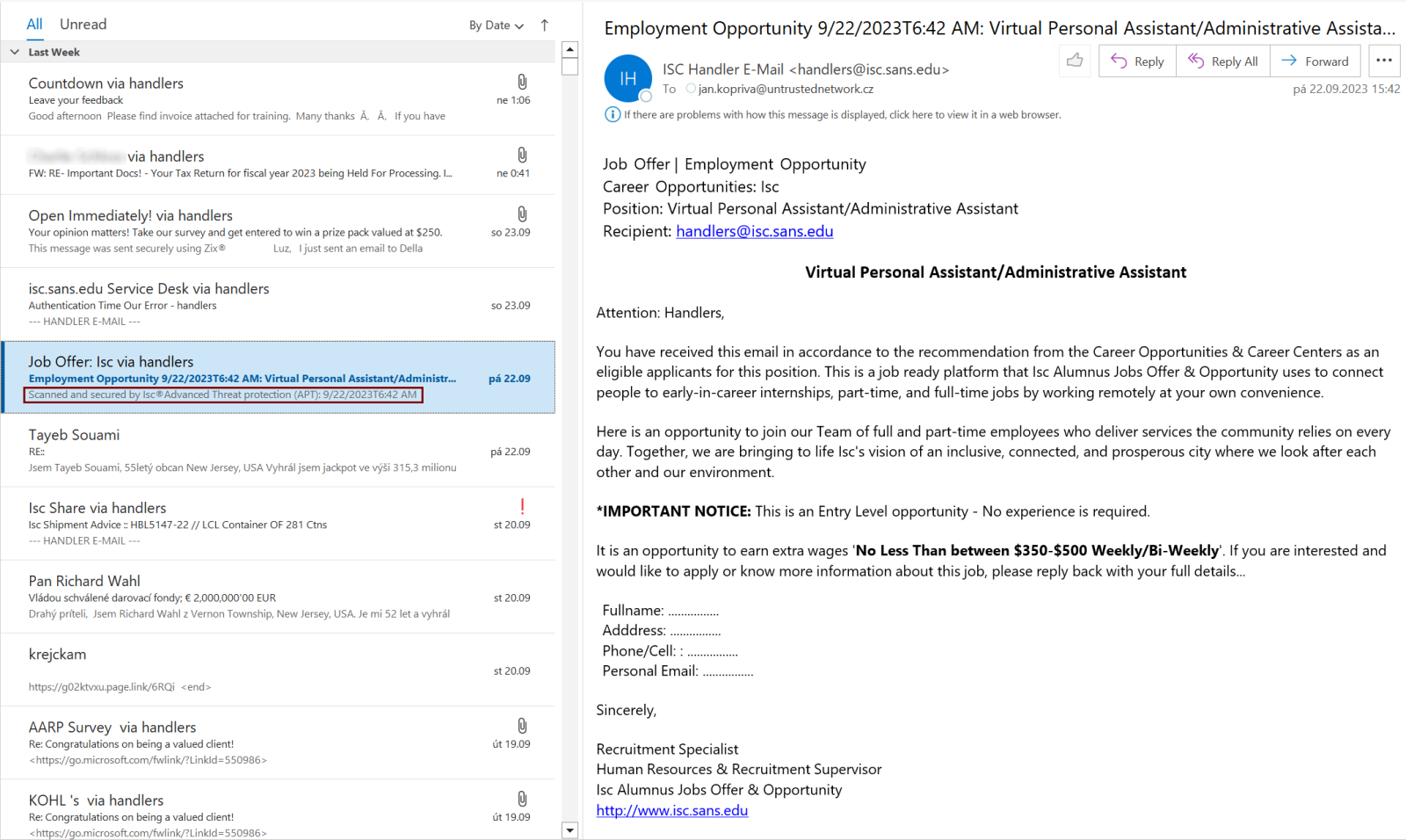
This discrepancy is achieved by leveraging ZeroFont to hide the bogus security scan message at the start of the phishing email, so while it’s not visible to the recipient, Outlook still grabs it and displays it as a preview on the email listing pane.
Source: ISC Sans
The goal is to instill a false sense of legitimacy and security in the recipient.
By presenting a deceptive security scan message, the likelihood of the target opening the message and engaging with its content rises.
It is possible that Outlook isn’t the only email client that grabs the first portion of an email to preview a message without checking if its font size is valid, so vigilance is advised for users of other software, too.