The NFS protocol offers authentication methods like AUTH_SYS, which relies on untrusted user IDs, and Kerberos, providing cryptographic verification.
While Kerberos offers strong security, its Linux configuration can be complex, where emerging standards like RPC over TLS aim to simplify secure NFS access by leveraging TLS for authentication and encryption, similar to HTTPS.
NFS servers restricted client connections to specific ports, requiring root privileges or special capabilities, which aimed to limit access and prevent unauthorized connections.

While Kerberos authentication can bypass this restriction on Linux, Windows servers always accept connections from any port, making this security mechanism largely obsolete in modern environments.
Linux NFS servers use squashing to control access permissions, which maps incoming user IDs to different IDs on the server, typically to enhance security.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
Common options include “all_squash” (squashes all IDs), “root_squash” (squashes root access only), and “no_root_squash” (allows root access), which helps address the issue of inconsistent user IDs between client and server systems.
NFS exports can restrict access to specific hosts using IP addresses, subnets, or hostnames, which can be granular, allowing different permissions for each host. While effective, security relies heavily on properly configured allowed networks and regular review of allowed IPs and hostnames.
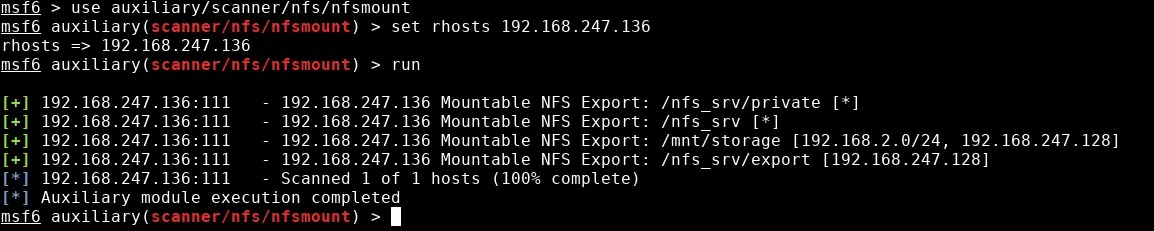
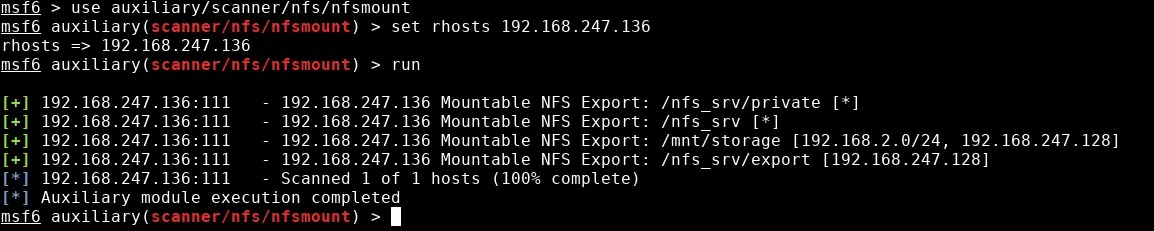
Linux systems utilize tools like `showmount` to gather information about NFSv3 servers, such as available exports, access permissions, and connected clients, which helps in understanding the server’s configuration.
For NFSv4, clients directly attempt to access exports under the `/` directory, with access control enforced at that level. The absence of export information from `showmount` often indicates an NFSv4-only server.
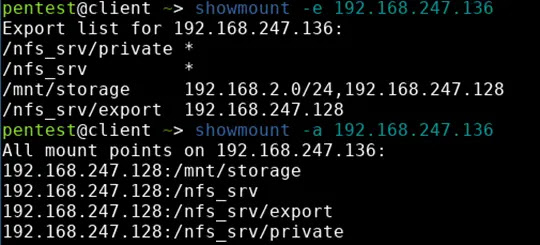
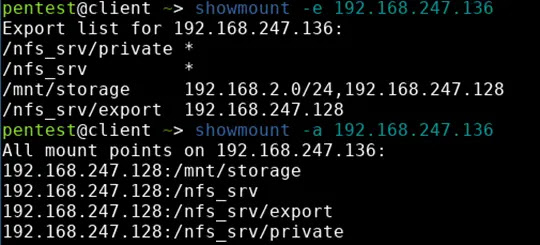
Existing NFS assessment tools, like Metasploit and nmap, lack comprehensive functionality. While effective, they often lack support for modern NFS versions like NFSv4, which necessitates more advanced techniques for identifying and accessing exports.
Leveraging NFS’s weak authentication (often relying on AUTH_SYS), attackers can exploit misconfigurations to gain unauthorized access to files on remote shares by impersonating users or groups with the necessary permissions, bypassing intended access controls.
fuse_nfs, a FUSE driver for NFS, enables unrestricted file access by automatically setting necessary user and group IDs for each file, allowing users to access files within their permissions on the NFS share, regardless of server-side authentication methods like Kerberos.
HVS Consulting analyzes NFS from an offensive perspective, highlighting common misconfigurations and vulnerabilities, which emphasizes the lack of adequate logging and detection mechanisms in Linux NFS implementations, making it challenging to identify and mitigate risks.
To secure NFS, restrict access to necessary clients, use NFSv4 with ACLs, export from root directories or enable subtree_check, avoid bind mounts and nested exports, mount with nosuid and nodev, disable no_root_squash, enable all_squash, prioritize Kerberos authentication, and use firewalls and network segmentation to control access.