Roughly 1,450 pfSense instances exposed online are vulnerable to command injection and cross-site scripting flaws that, if chained, could enable attackers to perform remote code execution on the appliance.
pfSense is a popular open-source firewall and router software that allows extensive customization and deployment flexibility. It is a cost-effective solution that accommodates specific needs, offering a wide range of features typically found in expensive commercial products.
In mid-November, SonarSource’s researchers with the aid of their SonarCloud solution discovered three flaws impacting pfSense 2.7.0 and older and pfSense Plus 23.05.01 and older. The flaws are tracked as CVE-2023-42325 (XSS), CVE-2023-42327 (XSS), and CVE-2023-42326 (command injection).
Although the reflected XSS flaws require user action on the victim’s side to work, the command injection flaw is more severe (CVSS score: 8.8).
This vulnerability in pfSense’s web UI arises from shell commands being constructed from user-provided data for configuring network interfaces without applying proper validation.
The flaw impacts the “gifif” network interface parameter, which isn’t checked for safe values, allowing malicious actors to inject additional commands in the parameter, leading to their execution with root privileges.
For this exploit to work, the threat actor needs access to an account with interface editing permissions, hence the need to chain the flaws together for a powerful attack.
Either CVE-2023-42325 or CVE-2023-42327 can be used for executing malicious JavaScript in an authenticated user’s browser to gain control over their pfSense session.
Netgate, the vendor of pfSense, received reports about the three flaws on July 3, 2023, and released security updates that addressed them on November 6 (pfSense Plus 23.09) and November 16 (pfSense CE 2.7.1).
However, a month after patches have been made available by Netgate, nearly 1,500 pfSense instances remain vulnerable to attacks.
Shodan scan results SonarSource’s researchers shared with BleepingComputer show that out of the 1,569 internet-exposed pfSense instances, 42 use pfSense Plus 23.09, and another 77 run pfSense Community Edition 2.7.1.
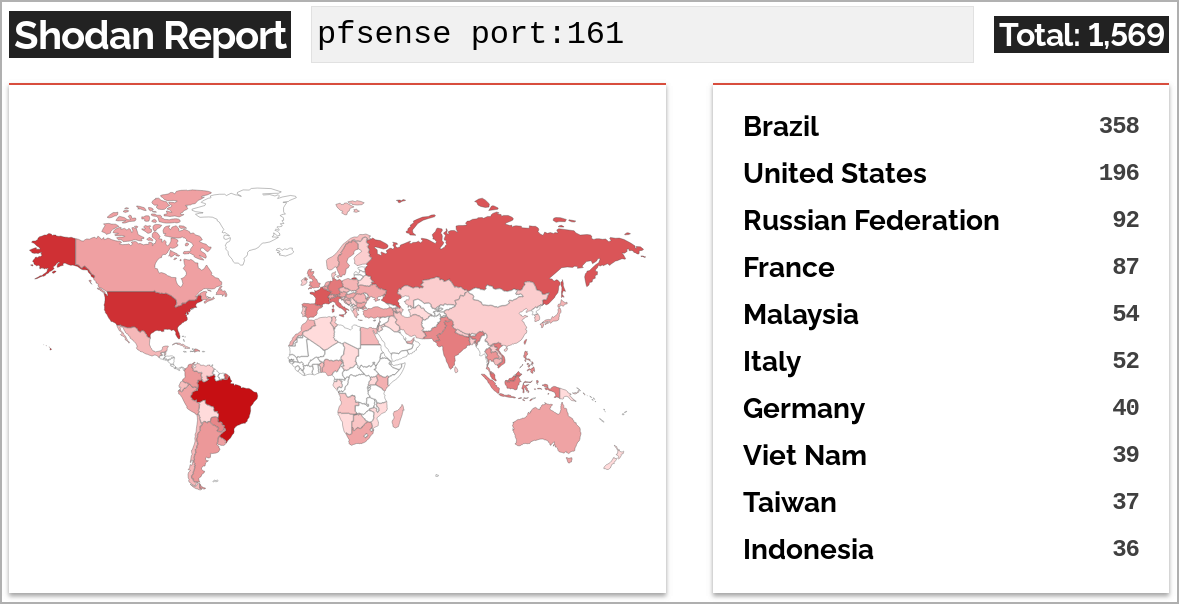
This leaves 1,450 instances (92.4%), which are directly discoverable through Shodan, vulnerable to the mentioned flaws.
While this exposure does not make these instances susceptible to immediate compromise, as threat actors would first need to target victims with XSS flaws, the exposure creates a significant attack surface.
While the number of vulnerable endpoints represents a small fraction of pfSense deployments globally, the fact that large enterprises often use the software makes this status particularly dangerous.
An attacker with access to pfSense operating with high-level privileges can easily cause data breaches, access sensitive internal resources, and move laterally within the compromised network.