Jul 09, 2025Ravie LakshmananMalware / Cyber Espionage A threat actor with suspected ties to India has been observed targeting a…
As part of the agreement, Google will train 100,000 civil servants working across the public sector in using AI and…
Still getting login codes via text or authenticator apps? You’re not alone—and that’s a big problem. What used to feel…
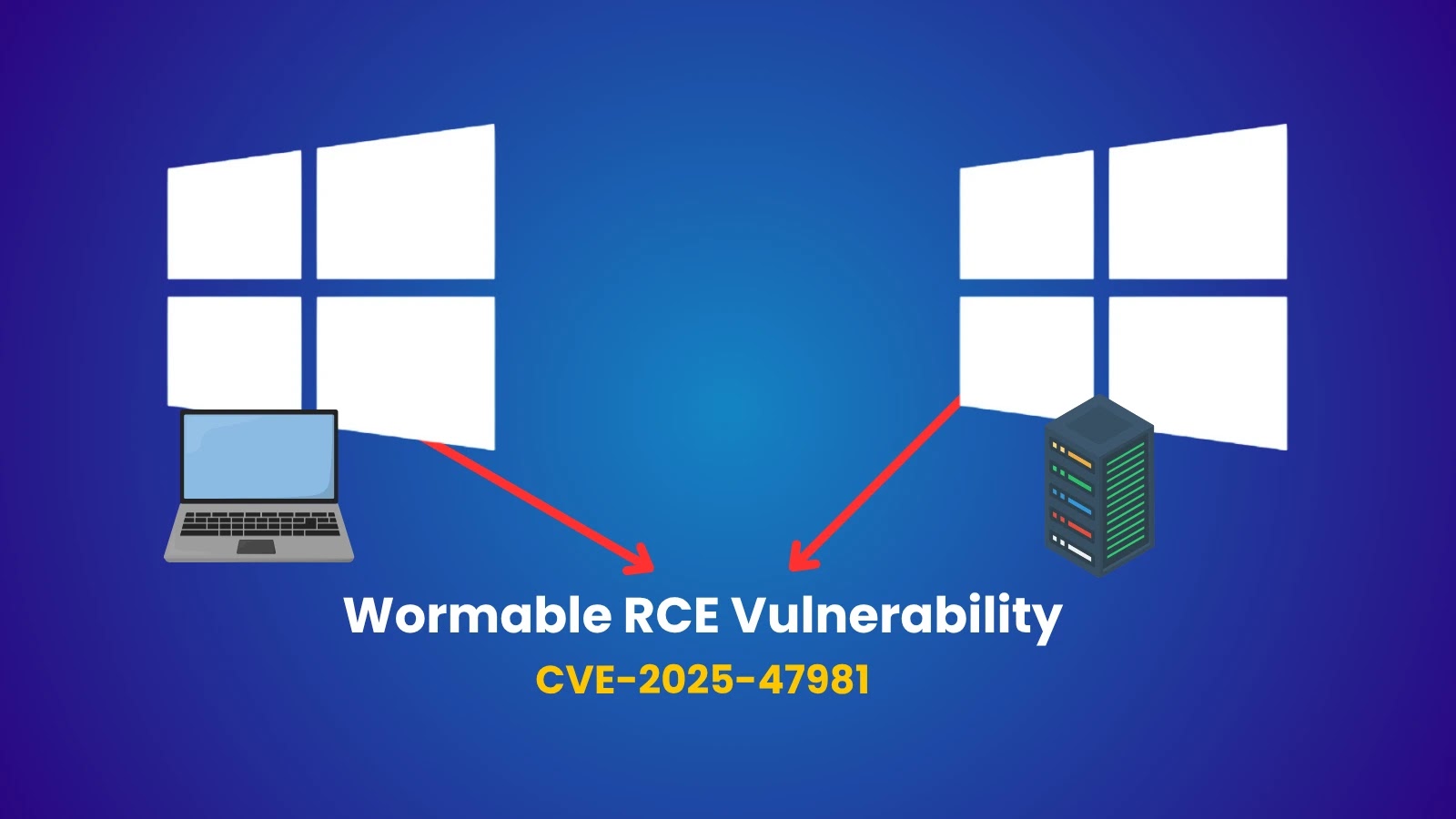
Microsoft has released critical security updates to address CVE-2025-47981, a severe heap-based buffer overflow vulnerability in the SPNEGO Extended Negotiation…
A sophisticated Trojan malware campaign has been targeting mobile device users across iOS and Android platforms since February 2024, with…
Iranian group Pay2Key.I2P ramps Up ransomware attacks against Israel and US with incentives for affiliates Pierluigi Paganini July 09, 2025…
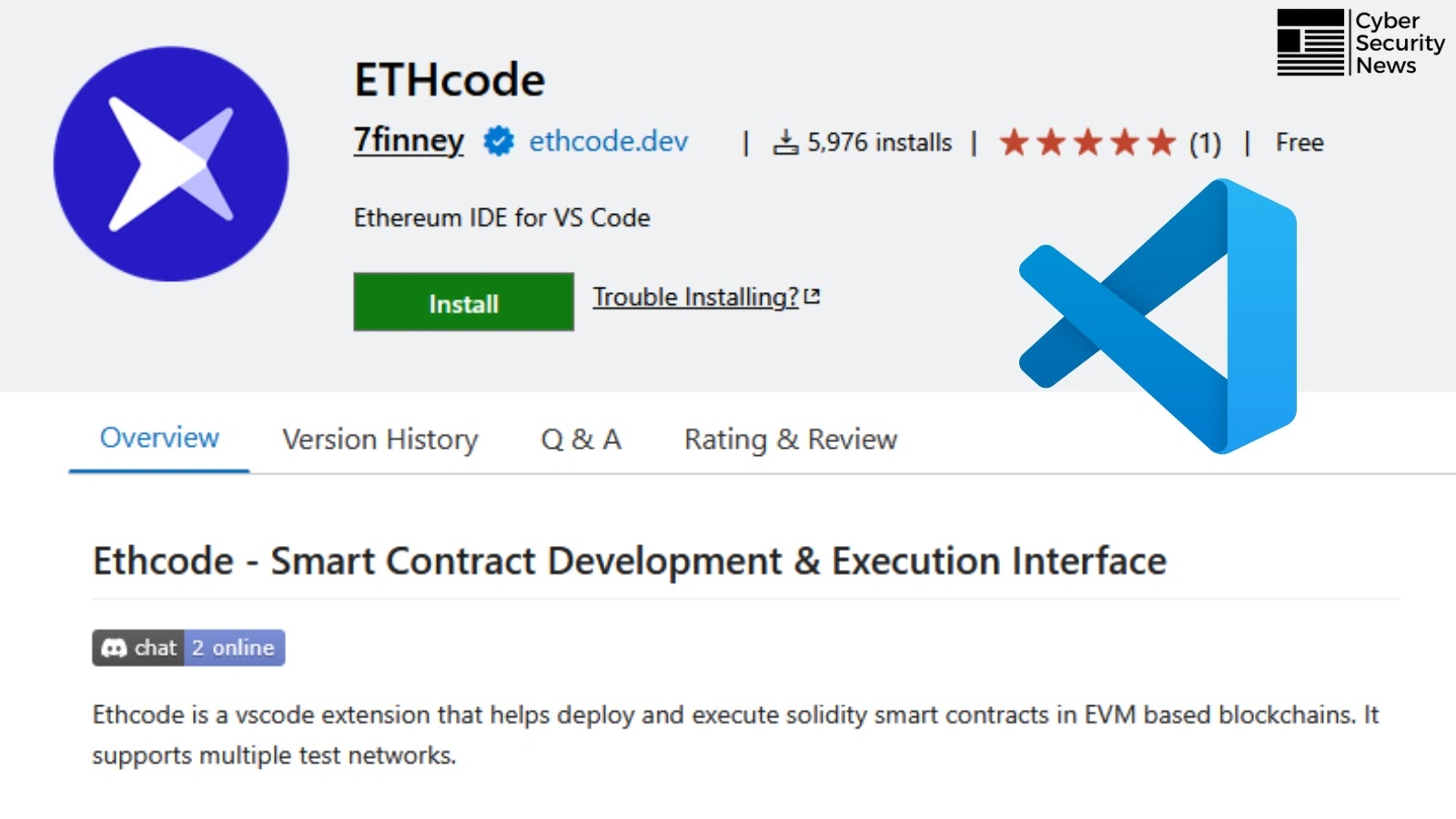
A sophisticated supply chain attack has compromised ETHcode, a popular Visual Studio Code extension for Ethereum development, through a malicious…
A new Android vulnerability called TapTrap that allows malicious apps to bypass the operating system’s permission system without requiring any…
Jul 09, 2025The Hacker NewsSecurity Operations / Automation Run by the team at workflow orchestration and AI platform Tines, the…
A sophisticated cyberattack orchestrated by Chinese state-sponsored hackers has exposed vulnerabilities in the global cybersecurity infrastructure, targeting critical COVID-19 research…
A sophisticated campaign by an initial access broker (IAB) group exploiting leaked Machine Keys from ASP.NET websites to gain unauthorized…
Adaptive Security provides one platform to prevent GenAI social engineering. The cybersecurity startup is upgrading the human firewall for deepfake personas,…