The BayMark Health Services, Inc. has reported a data breach to the California Attorney General, revealing that an unauthorized party…
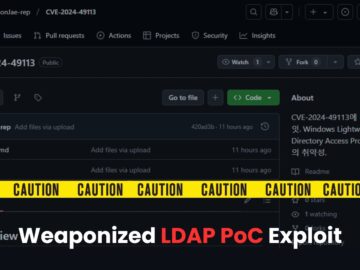
Security researchers are tricked into downloading and executing information-stealing malware by a fake proof-of-concept (PoC) exploit for CVE-2024-49113, dubbed LDAPNightmare….
In a sophisticated phishing campaign, uncovered cybercriminals are exploiting CrowdStrike’s recruitment branding to target developers and deploy the XMRig cryptominer….
Apple Inc. says its commitment to user privacy, emphasizing that its products, such as the digital assistant Siri, are designed…
A cyberattack, believed to have been launched by the Ukraine Cyber Alliance Group, is reported to have severely disrupted the…
Walker County Schools has reported that unauthorized access to personal data belonging to students and educators was achieved through the…
In this Help Net Security interview, Dr. Darren Williams, CEO at BlackFog, talks about how employee training plays a crucial…
Schools hold a special place in our communities, serving as the foundation for a child’s development and education. Yet, today’s…
Following the $95 million privacy breach settlement, Apple has clarified that Siri audio is not used for advertisements, remains private,…
The International Civil Aviation Organization (ICAO), a United Nations agency responsible for coordinating global aviation standards, has reported a significant…
As a company fortunate enough to have and maintain our own pentesting team, we often do outreach with other organizations…
Facebook has awarded a $100,000 bug bounty to security researcher Ben Sadeghipour for discovering a critical vulnerability in the company’s…