Microsoft is investigating a known issue triggering “Product Deactivated” errors for customers using Microsoft 365 Office apps. According to online…
NBN Co has revealed the cost of building lead-ins for 285,000 premises that upgraded from copper or fibre-to-the-curb to full…
Funds stolen by hacking cryptocurrency platforms surged 21 percent from a year ago to US$2.2 billion (A$3.5 billion) in 2024,…
Juniper Networks has warned customers of Mirai malware attacks targeting and infecting Session Smart routers using default credentials. As the…
A malicious Android spyware application named ‘BMI CalculationVsn’ was discovered on the Amazon Appstore, masquerading as a simple health tool…
Despite being taken down and humiliated by the National Crime Agency (NCA) coordinated Operation Cronos in February 2024, an unknown…
Fortinet has disclosed a critical vulnerability in Fortinet Wireless Manager (FortiWLM) that allows remote attackers to take over devices by…
The US government launched a national security investigation into the popular, Chinese-owned router maker TP-Link, with a potential eye on…
Microsoft has added another Windows 11 24H2 upgrade block for systems with Dirac audio improvement software due to compatibility issues…
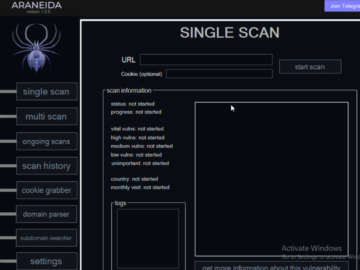
Cybercriminals are selling hundreds of thousands of credential sets stolen with the help of a cracked version of Acunetix, a…
The UK’s Competition and Markets Authority (CMA) sent shockwaves through the tech industry in October 2023 when it announced its…
Two amendments to the Data (Access and Use) Bill that would have established a statutory legal defence for security professionals…