With plans to offer more ransomware, LockBit has just created a variant for macOS. But, as experts have pointed out,…
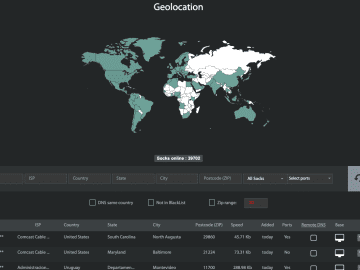
TL/DR: Just as vulnerabilities are constantly evolving, so must your approach to external attack surface monitoring. In addition to our…
Created/Updated: April 18, 2023 This is harder than it should be. Way harder. 0. Enable your terminal to make changes…
Within the Linux kernel, a security flaw that has been given the identifier CVE-2023-2002 has been discovered; this flaw poses…
How a simple scheduled job can help you quickly recover from ransomware. It’s 2019, and ransomware has become a thing….
This blog post is part 1 of an ongoing series that provide deep dives into HackerOne Assets and its core…
Numerous vulnerabilities have been found this week in Spring, a popular Java Web app development framework from VMware. Detectify Surface…
The US, UK, and Cisco are warning of Russian state-sponsored APT28 hackers deploying a custom malware named ‘Jaguar Tooth’ on…
A tour of brace expansion, shell parameter expansions, and playing with substrings in Bash. It’s that time of year again!…
There have been accusations on QuaDream, the Israeli firm using hacking tools for spying on journalists, opposition figures, and advocacy…
For the past seven years, a malware-based proxy service known as “Faceless” has sold anonymity to countless cybercriminals. For less…
CYFIRMA recently detected a cyber-attack on a person living in Kashmir, India, and obtained two malware pieces from the victim’s…