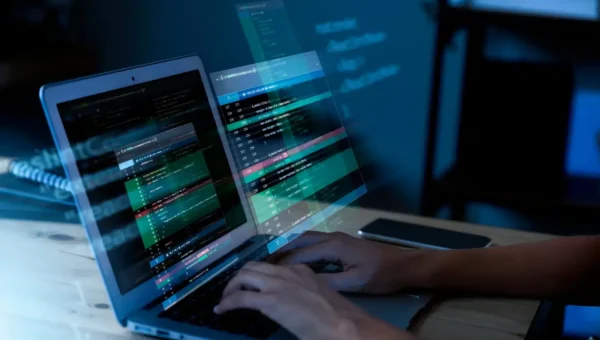
Cybercrime Is An Industrialized Economy
Cybercrime operates like a legitimate, profit-driven economy, writes Subhalakshmi Ganapathy, chief IT security evangelist at ManageEngine, in a BusinessWorld article. Organized groups mirror corporate structures and…