Flight Centre is hoping to cut the average handling time of customer inquiries in half by putting relevant data in…
WordPress plugin Jetpack released a critical security update earlier today, addressing a vulnerability that allowed a logged-in user to access…
Western Australia’s Department of Transport is recruiting for a CIO to uplift its IT and digital systems following an internal…
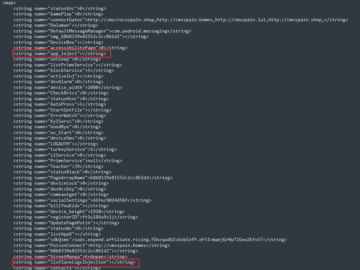
Cyble researchers have detected a sophisticated new variant of the Cerberus Android banking trojan that successfully evaded detection by antivirus…
Adobe has started publicly distributing an AI model that can generate video from text prompts, joining the growing field of…
Forty new variants of the TrickMo Android banking trojan have been identified in the wild, linked to 16 droppers and…
Researchers recently analyzed a CoreWarrior malware sample, which spreads aggressively by creating numerous copies and connecting to various IP addresses….
In July 2024, Central Tickets experienced a major data breach that compromised users’ personal information, including names, emails, phone numbers…
Nation-state actor exploited three Ivanti CSA zero-days Pierluigi Paganini October 14, 2024 An alleged nation-state actor exploited three zero-day vulnerabilities…
Earth Simnavaz, an Iranian state-sponsored cyber espionage group, has recently intensified its attacks on critical infrastructure in the UAE and…
TrickMo is a sophisticated malware that emerged as a “banking Trojan”, and this malware is designed to steal “financial credentials”…
It is evident that in the absence of vigilant oversight and corrective measures, situations can deteriorate rapidly, often leading to…