CrowdStrike said it has now sued Delta Air Lines in US District Court in Georgia after a faulty software update…
Microsoft announced today that inbound SMTP DANE with DNSSEC for Exchange Online, a new capability to boost email security and…
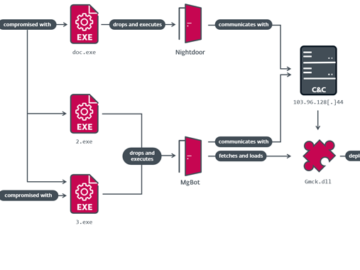
A hybrid espionage/influence campaign conducted by the Russian threat group ‘UNC5812’ has been uncovered, targeting Ukrainian military recruits with Windows…
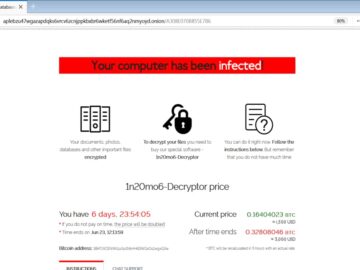
Four members of the notorious REvil ransomware group have been sentenced to prison terms in Russia. This development marks a…
28 Oct We Need to Talk: Breaking up with Your SIEM Vendor Posted at 13:54h in Blogs by Di Freeze…
Oct 28, 2024Ravie LakshmananCloud Security / Cyber Attack A government entity and a religious organization in Taiwan were the target…
Free, a major internet service provider (ISP) in France, confirmed over the weekend that hackers breached its systems and stole…
It’s often assumed that if the board knew exactly what they wanted to hear from the CISO, they would simply…
Last week, Greg Kroah-Hartman, the current maintainer of the stable branch of the open source Linux kernel, issued a message…
Cast your eye over the tech landscape and in all likelihood you will readily agree that the (data) clouds on…
The FBI and the U.S. Cybersecurity & Infrastructure Security Agency (CISA) have disclosed that Chinese hackers breached commercial telecommunication service…
In examining the global landscape of cyber fraud, it becomes evident that a significant proportion of victims are often educated…