In this Help Net Security interview, Alex Spivakovsky, VP of Research & Cybersecurity at Pentera, discusses essential metrics for evaluating…
Data breach episodes have been constantly rising with the number of data breach victims crossing 1 billion in the first…
92% of security leaders have concerns about the use of AI-generated code within their organization, according to Venafi. Tension between…
In a recent cyberattack, Russian cybersecurity firm Doctor Web (Dr.Web) was forced to disconnect all its servers to mitigate the…
Today, I stumbled upon an interesting quirk while working on a Chrome Extension project using LazyVim. It’s a classic case…
The FBI, in collaboration with U.S. government agencies, dismantled a Chinese state-backed botnet known as Flax Typhoon, comprising 260,000 compromised…
With Gartner recently declaring that SOAR (security orchestration, automation, and response) is being phased out in favor of generative AI-based…
Discord has introduced the DAVE protocol, a custom end-to-end encryption (E2EE) protocol designed to protect audio and video calls on…
A VPN (Virtual Private Network) adds privacy and security to your browsing. But does this make your internet activity truly…
On Tuesday, Russian anti-malware company Doctor Web (Dr.Web) disclosed a security breach after its systems were targeted in a cyberattack…
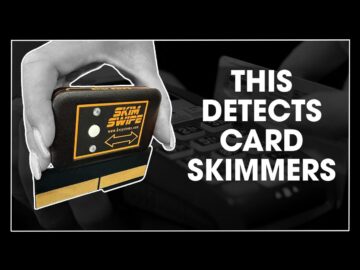
18 Sep Product Review: Skim Swipe POS Retail Terminal Card Skimmer Detector Posted at 17:01h in Blogs, Videos by Di…
Europol and law enforcement from nine countries successfully dismantled an encrypted communications platform called “Ghost,” which was used by organized crime…