Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support…
I. INTRODUCTION Endpoint Detection & Response (EDR) systems often use the ProcessParameters field of the Process Environment Block (PEB) to…
Deutsche Unternehmen müssen sich warm anziehen: Sowohl staatliche als auch „private“ Akteure haben es auf sie abgesehen. Shutterstock Wie die…
According to independent researcher Kevin Beaumont, three organizations told him that devices inside their networks that had Notepad++ installed experienced…
Amazon Web Services (AWS) is pleased to announce the successful completion of Payment Card Industry Personal Identification Number (PCI PIN)…
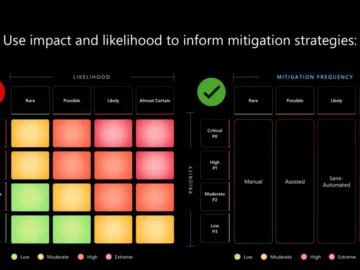
Proactively identifying, assessing, and addressing risk in AI systems We cannot anticipate every misuse or emergent behavior in AI systems….
Microsoft’s February 2026 Patch Tuesday focuses on closing security gaps that attackers could exploit, reinforcing the importance of timely patching in enterprise environments. Here’s a quick breakdown of what you need to know. Microsoft…
Athanasios Rantos, the Advocate General of the Court of Justice of the EU (CJEU), has issued a formal opinion suggesting…
Tired of repeating yourself? Automate your web security audit trail. In this post I’ll introduce a new Burp AI extension…
Ravie LakshmananMar 04, 2026Vulnerability / Enterprise Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a recently…
I. INTRO Important or sensitive processes of modern Windows operating systems are now protected by the Protected Process Light…
Das sieht auch Toby Basalla, Gründer und Principal Data Consultant bei Synthelize, so. “Wenn Chaos herrscht, wer weiß dann noch,…