Organizations must reassess their email security posture as incidents continue to escalate, leading to financial losses. Key findings reveal a…
Fortinet, a leading cybersecurity firm, has confirmed a data breach involving a third-party cloud service after a hacker, known by…
Infrastructure as Code (IaC) has become a widely adopted practice in modern DevOps, automating the management and provisioning of technology…
SquareX has been named a winner of the prestigious Rising Star category in CybersecAsia Readers’ Choice Awards 2024 Awards, due…
SquareX has been named a winner of the prestigious Rising Star category in CybersecAsia Readers’ Choice Awards 2024 Awards, due…
Organizations are grappling with their current NHI (non-human identities) security strategies, according to Cloud Security Alliance and Astrix Security. The…
Singapore, Singapore, September 13th, 2024, CyberNewsWire SquareX has been named a winner of the prestigious Rising Star category in CybersecAsia…
Singapore, Singapore, September 13th, 2024, CyberNewsWire SquareX has been named a winner of the prestigious Rising Star category in CybersecAsia…
Cyber insurance is poised for exponential growth over the coming decade, but it remains a capital-intensive peril that requires structural…
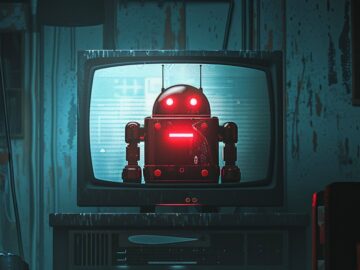
Image: Midjourney Threat actors have infected over 1.3 million TV streaming boxes running Android with a new Vo1d backdoor malware,…
Ericsson has created a new company for selling network software tools it has created a joint venture to sell software…
Prevention is always better than a cure, but no proactive measure is foolproof. Cyberattacks are too frequent and the consequences…