Large-scale IT outages in Australia and globally are being linked to a problem within an endpoint security service made by…
Microsoft says an Azure configuration change caused a major Microsoft 365 outage on Thursday, affecting customers across the Central US…
Hewlett Packard Enterprise (HPE) has addressed a critical vulnerability in its 3PAR Service Processor software that could have far-reaching implications…
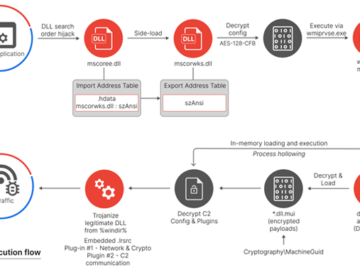
Jul 19, 2024NewsroomCyber Espionage / Threat Intelligence Several organizations operating within global shipping and logistics, media and entertainment, technology, and…
Bassett Furniture Industries has disclosed a major cyberattack that has severely disrupted its operations. The Virginia-based company revealed in a…
We’re gearing up with some seriously cool stuff for Black Hat! But first, a little sneak peek – not just…
A recent update to the CrowdStrike Falcon sensor is causing major issues for Windows users worldwide. This update is leading…
Banks, airports, TV stations, hotels, and countless other businesses are all facing widespread IT outages, leaving flights grounded and causing…
A recent update from cybersecurity firm CrowdStrike has caused significant disruptions for Windows users, leading to widespread reports of Blue…
Houndreds of housands and possibly millions of Windows computers and servers worldwide have been made inoperable by a faulty update…
Jul 19, 2024The Hacker NewsTechnology / Artificial Intelligence Event Overview The “AI Leaders Spill Their Secrets” webinar, hosted by Sigma…
The cyberattack on India’s biggest cryptocurrency exchange WazirX has sent shockwaves through the crypto community. The WazirX hack on July…