FireTail announces a free version of its enterprise-level API security tools, making them accessible to developers and organizations of all…
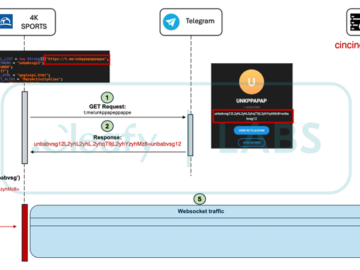
Jun 26, 2024NewsroomAndroid Security / Threat Intelligence Cybersecurity researchers have discovered an updated version of an Android banking trojan called…
Gaby Portnoy, director general of the Israel National Cyber Directorate (INCD), has called for countries to work together in a…
The Health Sector Cybersecurity Coordination Center (HC3) has issued a critical alert regarding a new ransomware strain, Qilin, which is…
McLean, United States of America, June 26th, 2024, CyberNewsWire FireTail announces a free version of its enterprise-level API security tools,…
With the rise of digital transformation and widespread adoption of cloud-based solutions, organizations are increasingly turning to these platforms to…
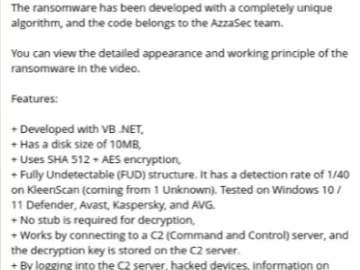
Hacktivist group AzzaSec has announced the release of a Windows ransomware builder. The builder was posted via the Telegram channel…
A range of ICT and enterprise software vendors could face government scrutiny over how they “cultivate” relationships with agency officials…
Cybersecurity researchers have discovered a significant evolution in the previously dormant P2Pinfect malware strain. The updated version can now deploy…
Microsoft has announced the general availability of Copilot for Security threat intelligence embedded experience in the Defender XDR portal. This…
Safeguarding oneself from sectortion attacks online is crucial in today’s digital age where cyber threats continue to evolve. Se*tortion, a…
The Federal Bureau of Investigation (FBI) has warned the public about a new wave of cybercriminal activity targeting victims of…