The Forminator WordPress plugin used in over 500,000 sites is vulnerable to a flaw that allows malicious actors to perform unrestricted…
A French hospital was forced to reschedule procedures after cyberattack Pierluigi Paganini April 20, 2024 A French hospital was forced…
By David Lee, Chief Evangelist and Visionary for Tech Diversity As technology rapidly evolves and advances, it can often seem…
20 Apr Lessons Learned From Recent Ransomware Attacks Posted at 08:26h in Blogs by Di Freeze This week in cybersecurity…
Looking for love? Be careful what you wish for. A loose-knit community of con artists known as Yahoo Boys has…
The MITRE Corporation, a non-profit organization that runs federally funded research and development centers, has disclosed that a sophisticated cyber…
Trust is perhaps the most foundational principle that shapes how businesses operate. It’s important to customers, partners, employees, and just…
Apr 20, 2024NewsroomVulnerability / Endpoint Security Users of the CrushFTP enterprise file transfer software are being urged to update to…
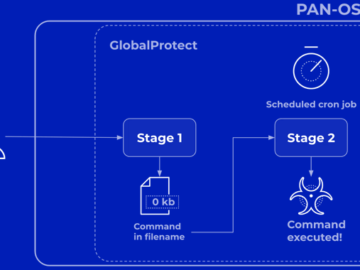
Apr 20, 2024NewsroomVulnerability / Network Security Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS…
While ransomware attacks decreased after the LockBit and BlackCat disruptions, they have once again started to ramp up with other…
MITRE revealed that nation-state actors breached its systems via Ivanti zero-days Pierluigi Paganini April 19, 2024 The MITRE Corporation revealed…
CrushFTP warned customers today in a private memo of an actively exploited zero-day vulnerability fixed in new versions released today,…