Anthropic has filed a lawsuit to block the Pentagon from placing it on a national security blacklist, escalating the artificial…
Security awareness training (SAT) is supposed to make companies safer, but too often, it feels like just another box to…
Hackers contacted employees at financial and healthcare organizations over Microsoft Teams to trick them into granting remote access through Quick Assist…
Microsoft has introduced Copilot Cowork, a new AI-powered feature embedded within Microsoft 365 that moves beyond conversational assistance to autonomous…
Russian-backed hackers have launched a global cyber campaign to gain access to Signal and WhatsApp accounts used by officials, military…
Download the full report The 2026 State of Security report provides comprehensive analysis of each threat domain, threat actor profiles,…
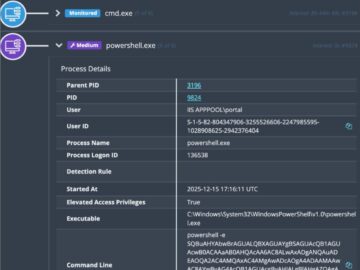
Acknowledgments: Special thanks to John Hammond for his contributions to this investigation and write-up. Update #2: 12/18/25 @ 6pm ET…
Hackers are increasingly exploiting newly disclosed vulnerabilities in third-party software to gain initial access to cloud environments, with the window…
A new data-stealing malware called BoryptGrab has been quietly spreading across Windows systems through a network of fake GitHub repositories,…
For years, tech companies successfully resisted pressure from child safety advocates to do more to keep kids off their services, claiming…
FBI alert: scammers target zoning permit applicants Pierluigi Paganini March 09, 2026 The FBI warns of phishing attacks where crooks…
Listen to the article 2 min This audio is auto-generated. Please let us know if you have feedback. WASHINGTON — The…