[ This article was originally published here ] This is equivalent to 20,000 tons of polymers – the weight of…
Attackers behind an ongoing series of proxyjacking attacks are hacking into vulnerable SSH servers exposed online to monetize them through…
[ This article was originally published here ] Highlights taken from , for the As organisations and Governments look…
[ This article was originally published here ] Podcasts have undergone a full-blown renaissance in recent years. Whether it’s high-profile…
Iran-linked Charming Kitten group used an updated version of the PowerShell backdoor called POWERSTAR in a spear-phishing campaign. Security firm…
[ This article was originally published here ] Did you know that tattoos were some of the first forms of…
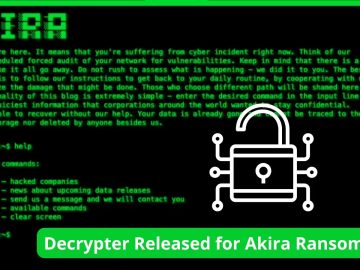
Cybersecurity firm Avast has released a free decryptor for the Akira ransomware that can help victims recover their data without…
Akira ransomware appeared in 2017 when it encrypted video folders without leaving any ransom notes. The file encrypted by Akira…
[ This article was originally published here ] If you’ve read part one, you’ll know that there’s a persistent problem…
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned today of ongoing distributed denial-of-service (DDoS) attacks after U.S. organizations across…
The DPRK campaign is utilizing a recently updated version of Rustbucket malware to avoid being detected. This variant of RUSTBUCKET,…
The sudden surge in the activity of 8base ransomware in June 2023 shows it is a well-established organization to execute…