Google said it would be “extremely difficult” for Australia to enforce a law prohibiting people younger than 16 from using…
I. STARTER When conducting penetration testing on target machines, our actions will be ruthlessly monitored and judged by Antivirus….
Oct 13, 2025Ravie LakshmananBrowser Security / Windows Security Microsoft said it has revamped the Internet Explorer (IE) mode in its…
As the cyber threat landscape down under intensifies, Australia has launched CI Fortify, a comprehensive guidance framework designed to help…
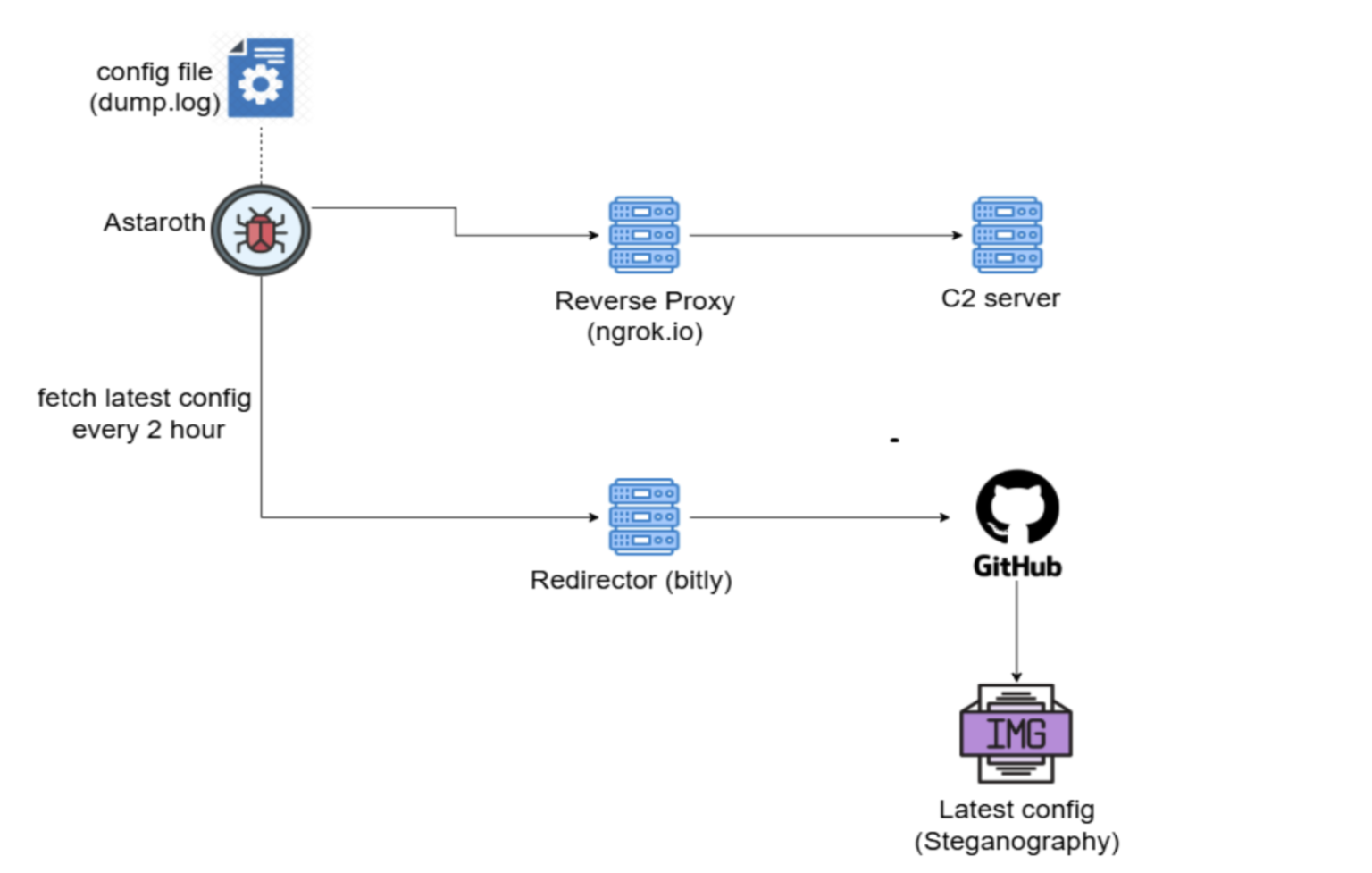
Astaroth Trojan abuses GitHub to host configs and evade takedowns Pierluigi Paganini October 13, 2025 The Astaroth banking Trojan uses…
A recent analysis from researcher Itamar Hällström has revealed the technical workings and forensic trail of “EDR-Freeze,” a proof-of-concept technique…
North Korean threat actors have escalated their Contagious Interview campaign, deploying 338 malicious npm packages with over 50,000 downloads to…
Malware campaigns distributing the RondoDox botnet have expanded their targeting focus to exploit more than 50 vulnerabilities across over 30…
The United Arab Emirates (UAE) will have 10,000 artificial intelligence (AI) companies in five years’ time, up from 1,500 currently….
McAfee’s Threat Research team recently uncovered a sophisticated new Astaroth campaign that represents a significant evolution in malware infrastructure tactics….
UK police are building a new system to help fight economic crime and improve the tracking, management and recovery of…
A sophisticated new malware campaign targeting Windows systems has emerged, leveraging Node.js Single Executable Application (SEA) features to distribute malicious…