The Phishing-as-a-Service Pipeline: How a Scalable Fraud Ecosystem Is Driving Global Attacks
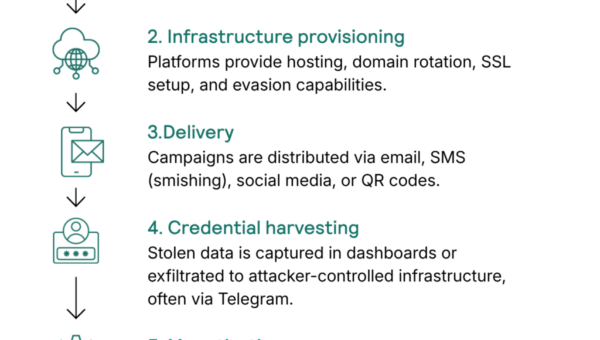
Phishing is no longer a standalone tactic. It has matured into a service-based ecosystem where specialized actors provide each component of an attack lifecycle, from…