Phishing campaign targeted US executives exploiting a flaw in Indeed job search platform

Threat actors exploited an open redirection vulnerability in the job search platform Indeed to carry out phishing attacks.
Researchers from the cybersecurity firm Menlo Security reported that threat actors exploited an open redirection vulnerability in the job search platform Indeed in phishing attacks.
The phishing attacks were aimed at senior executives across various industries, primarily in Banking, Financial, Insurance, Property Management and Real Estate, and Manufacturing sectors.
The campaign was observed between July and August, threat actors used the phishing kit ‘EvilProxy.’ EvilProxy actors are using Reverse Proxy and Cookie Injection methods to bypass 2FA authentication – proxyfying victim’s session.
The attackers exploited the open redirection vulnerability on “indeed.com” to redirect victims to phishing pages impersonating Microsoft.
The fake Microsoft Online login page is deployed with the EvilProxy framework fetching all the content dynamically from the legitimate login site.

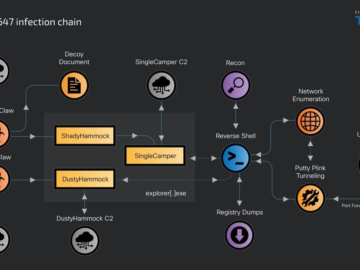
The phishing site acts as a reverse proxy, proxying the request to the actual website. Thereat actors are able to intercept the legitimate server’s requests & responses and steal the session cookies. Then the cookies are used by the attackers to login to take over the victims’ account on the legitimate Microsoft Online site, bypassing non-phishing resistant MFA.
“In this specific attack, the user clicks on a URL believing that they are being directed to indeed.com or another of its subdomains. The subdomain ‘t.indeed.com’ is supplied with parameters to redirect the client to another target (example.com) as shown in the example below.” states the report from Menlo Security. “The parameters in the URL that follow the “?” are a combination of parameters unique to indeed.com and the target parameter whose argument consists of the destination URL. Hence the user upon clicking the URL ends up getting redirected to example.com. In an actual attack, the user would be redirected to a phishing page.”

The attackers used the subdomain ‘lmo.’ and hosted the phishing pages on nginx servers that were used as reverse proxies.
“The phishing pages were found to be hosted on nginx servers capable of acting as a reverse proxy. The reverse proxy fetches all the content that can be dynamically generated like the login pages and then acts as the adversary in the middle by intercepting the requests and responses between the victim and the legitimate site.” continues the report. “This helps in harvesting the session cookies and this tactic can be attributed to the usage of EvilProxy Phishing kit.”
Menlo Security shared its findings with Indeed, the researchers conclude that there is a high probability that we can see a surge in the usage of ‘EvilProxy.’
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, phishing)