Play ransomware attack on Xplain exposed 65,000 files containing data relevant to the Swiss Federal Administration.

The ransomware attack on Xplain impacted tens of thousands Federal government files, said the National Cyber Security Centre (NCSC) of Switzerland.
The National Cyber Security Centre (NCSC) published a data analysis report on the data breach resulting from the ransomware attack on the IT services provider Xplain. The attack took place on May 23, 2023 and the Play ransomware gang claimed responsibility for the data breach.
In early June, Swiss police launched an investigation into the cyberattack that targeted the Bernese IT company Xplain. Xplain provides its services to several federal and cantonal government departments, the army, customs, and the Federal Office of Police (Fedpol).
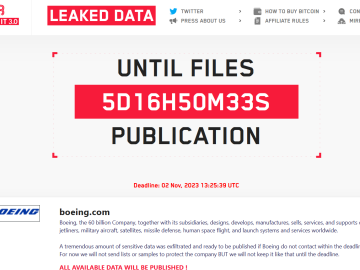
Threat actors initially published alleged stolen data from the Federal Office of Police (Fedpol) and the Federal Office for Customs and Border Security (FOCBS) on a Darknet forum.
Local media reported that attackers exploited a vulnerability on the servers of the company.
Both Fedpol and the federal customs office confirmed the attack but attempted to downplay the incident. According to Fedpol, threat actors only had access to simulated, anonymous data for test purposes.
The Federal Office for Customs and Border Security (FOCBS) said data from the FOCBS that were exposed are from correspondence with its clients.
According to the data analysis report, the Play ransomware gang published the stolen data on the darknet on 14 June 2023. The data exfiltrated by the gang included classified information and sensitive personal data from the Federal Administration.
Threat actors stole and leaked roughly 1.3 million files, and 65,000 documents were classified by NCSC as data relevant to the Federal Administration.
Most of the stolen files belonged to Xplain (47,413) with a share of over 70%; around 14% (9,040) belonged to the Federal Administration.
“Around 95% of the Federal Administration’s files belonged to the administrative units of the Federal Department of Justice and Police (FDJP): the Federal Office of Justice, Federal Office of Police, State Secretariat for Migration and the internal IT service centre ISC-FDJP. With just over 3% of the data, the Federal Department of Defence, Civil Protection and Sport (DDPS) is slightly affected and the other departments are only marginally affected in terms of volume.” reads the report.
Government experts discovered sensitive information, including personal data, technical information, classified details, and passwords, in approximately half of the Federal Administration’s files (5,182).
4,779 Federal Administration’s files contained personal data such as names, email addresses, telephone numbers, and postal addresses.
278 Federal Administration’s files contained technical information, encompassing documentation on IT systems, software requirement documents, or architectural descriptions. Additionally, 121 objects were classified in accordance with the Information Protection Ordinance, and 4 objects contained readable passwords.”
“In addition, 278 files contained technical information such as documentation on IT systems, software requirement documents or architectural descriptions, 121 objects were classified in accordance with the Information Protection Ordinance and 4 objects contained readable passwords.” continues the report.
“On August, the Government launched an administrative investigation into the data breach. This investigation is expected to be completed by the end of March 2024.”
“A considerable amount of analysis was required to determine how much data was leaked and the owners of the leaked data. Suitable tools were required to process unstructured data records and make their contents readable.” concludes the announcement. “The objects identified as relevant then had to be manually viewed and categorised. The various federal offices and service providers involved worked closely under the lead of the NCSC to manage the security incident. This allowed all parties to utilise synergies, make effective use of resources and save valuable time.”
Follow me on Twitter: @securityaffairs and Facebook
Pierluigi Paganini
(SecurityAffairs – hacking, Xplain)