Prometei botnet activity has surged since March 2025

Prometei botnet activity has surged since March 2025, with a new malware variant spreading rapidly, Palo Alto Networks reports.
Palo Alto Networks warns of a spike in Prometei botnet activity since March 2025, the researchers observed a new variant spreading rapidly.
Since March 2025, Prometei botnet is targeting Linux systems for Monero mining and credential theft. The bot is under active development and uses a modular architecture, domain generation algorithms, and self-updating features to evade detection.
“This malware family, which includes both Linux and Windows variants, allows attackers to remotely control compromised systems for cryptocurrency mining (particularly Monero) and credential theft. This article focuses on the resurgence of the Linux variant.” reads the report published by Palo Alto Networks. “Prometei is under active development, incorporating new modules and methods into its capabilities. The latest Prometei versions feature a backdoor that enables a variety of malicious activities. “
The malware was first discovered in 2020, it exploits vulnerabilities like EternalBlue and SMB flaws. Prometei spreads via brute-force and deploys multiple payloads, showing strong persistence but no state ties.
Prometei primarily mines Monero but also steals credentials and deploys other malware. Its activity appears financially motivated, with no nation-state ties.
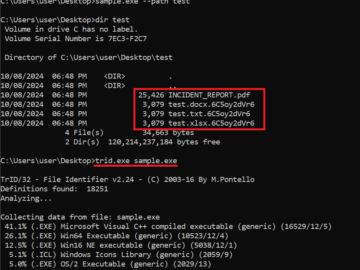
The most recent variant of the bot is distributed via an HTTP GET request, delivering a UPX-packed 64-bit Linux ELF file disguised as a .php script. It uses dynamic ParentID values and randomized configurations. The hosting server, based in Indonesia, runs Apache on Windows. The 2025 versions support UPX compression to obfuscate the malware, which decompresses at runtime to execute its payload.

Prometei’s malware is packed with Ultimate Packer for eXecutables (UPX), but standard unpacking fails due to an appended JSON config trailer. To analyze it statically, analysts must strip this trailer, unpack the sample, then reattach the JSON. This config holds fields like ParentId, ParentIp, and encryption keys.
“The sample contains a subroutine to search for and parse the configuration JSON trailer.” continues the report. “The sample also contains another subroutine responsible for collecting compromised system information. This information includes:
- Processor information (obtained from /proc/cpuinfo)
- Motherboard information (obtained using the dmidecode –type baseboard command)
- Operating system information (obtained from /etc/os-release or /etc/redhat-release)
- Information about how long the system has been running (obtained using the uptime command)
- Kernel information (obtained using the uname -a command)”
The Prometei botnet is resurging with evolved evasion techniques. It can be detected using a YARA rule targeting UPX and its config JSON trailer, but defenders must stay vigilant as it continues to adapt.
The report includes Indicators of Compromise (IoCs).
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, malware)