Ransomware payments rose from $449.1 million to $459.8 million
Blockchain analysis firm Chainalysis revealed that ransomware payments rose by approximately 2%, from $449.1 million to $459.8 million.
Blockchain analysis firm Chainalysis revealed that while overall on-chain illicit activity has decreased by nearly 20% year-to-date, stolen funds and ransomware significantly increased. Stolen funds inflows almost doubled, rising from $857 million to $1.58 billion, and ransomware inflows grew by about 2%, from $449.1 million to $459.8 million.
In 2024, ransomware payments are on track to reach record highs, driven by “big game hunting,” the experts believe that fewer but more high-profile attacks result in larger ransoms. The largest ransom payment recorded this year was $75 million to the Dark Angels ransomware group.

The experts pointed out that the growing trend of increasing ransomware payments is particularly alarming, with both maximum and median payment amounts rising sharply, especially for the most severe ransomware strains. These strains, classified based on their on-chain activity, show a significant increase in median payments, particularly for “very high severity” strains. For instance, the median payment for these strains skyrocketed from $198,939 in early 2023 to $1.5 million by mid-2024, representing a nearly 8-fold increase in just 18 months and a 1200-fold rise since early 2021.
These figures demonstrated that ransomware gangs focus on larger businesses and critical infrastructure.
Despite law enforcement disruptions causing fragmentation in the ransomware ecosystem, crypto adoption has grown, with positive developments like ETF approvals.
Disruptions of the largest ransomware operations, like ALPHV/BlackCat and LockBit, lead to the migration of the affiliates to less effective strains or the rebranding of some operations.
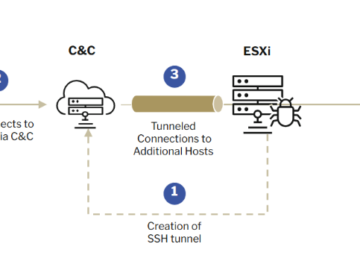
“Whether it be former affiliates of these well-known threat actor operations, or new upstarts, a large number of new ransomware groups have joined the fray, displaying new methods and techniques to carry out their attacks such as expansion in their means for initial access and lateral movement approaches.” said Andrew Davis, general counsel at Kiva Consulting.
“This encouraging sign points to the continued adoption of crypto globally. Inflows to risky services (made up primarily of mixers and exchanges that do not collect KYC information) are trending higher than they were at this point last year. Meanwhile, aggregate illicit activity fell YTD by 19.6%, dropping from $20.9B to $16.7B, demonstrating that legitimate activity is growing faster than illicit activity on-chain.” states the report.

Ransomware attacks have increased by at least 10% this year, according to data from eCrime.ch. Despite this surge and a record high in ransom volumes and maximum payment sizes, the good news is that victims are paying ransoms less frequently. While ransomware incidents posted on leak sites have risen by 10% year-over-year, on-chain data shows a 27.29% decline in actual ransom payments. Summarizing, although more victims are being targeted, fewer are paying.
“The key to disrupting cybercrime is disrupting its supply chains, including attackers, affiliates, partners, infrastructure services providers, launderers, and cashout points.” concludes the report. “Because the operations for crypto heists and ransomware operate almost entirely on the blockchain, law enforcement armed with the right solutions can follow the money to better understand and disrupt these actors’ operations”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, malware)