Midnight Blizzard – a cyber espionage group that has been linked to the Russian Foreign Intelligence Service (SVR) – is targeting government, academia, defense, and NGO workers with phishing emails containing a signed Remote Desktop Protocol (RDP) configuration file.
“Based on our investigation of previous Midnight Blizzard spear-phishing campaigns, we assess that the goal of this operation is likely intelligence collection,” Microsoft’s threat analysts say.
Midnight Blizzard
Midnight Blizzard (aka Cozy Bear, APT29, and UNC2452) has been implicated in a number of high-profile attacks in the last decade or so:
“Midnight Blizzard is consistent and persistent in its operational targeting, and its objectives rarely change,” Microsoft notes.
“It uses diverse initial access methods, including spear phishing, stolen credentials, supply chain attacks, compromise of on-premises environments to laterally move to the cloud, and leveraging service providers’ trust chain to gain access to downstream customers. Midnight Blizzard is known to use the Active Directory Federation Service (AD FS) malware known as FoggyWeb and MagicWeb.”
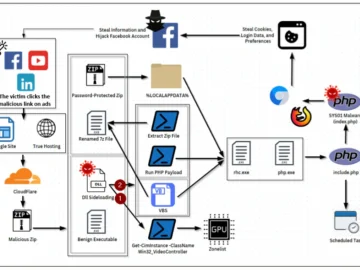
The spear-phishing campaign
The group’s spear-phishing tactics are always changing. Last year, for example, have been spotted trying to phish government employees via Microsoft Teams.
In this latest campaign, which is still ongoing, Midnight Blizzard tries to trick targets into downloading and opening a RDP configuration file (.rdp).
The emails are sent from legitimate email addresses that were compromised in previous attacks. The thousands of targeted recipients are employees of governmental agencies, higher education, defense, and non-governmental organizations in dozens of countries, including the UK, Europe, Australia, and Japan.
As the Ukrainian CERT team recently warned, running the malicious file will establish an outgoing RDP connection with the attackers’ server, allowing the server access to disks, network resources, printers, COM ports, audio devices, the clipboard and other resources (including credentials) on the targets’ computer, as well as put into place technical prerequisites for running third-party programs or scripts.
The prompts shown when running the malicios file (Source: Microsoft)
“The emails were highly targeted, using social engineering lures relating to Microsoft, Amazon Web Services (AWS), and the concept of Zero Trust,” Microsoft says.
Amazon shared that some of the domain names they used tried to trick the targets into believing the domains were AWS domains, and that the company initiated the process of seizing them.
CERT-UA advised blocking RDP files on the mail gateway, blocking users from running RDP files (with exeptions), and configuring the firewall to limit the possibility of establishing RDP connections by the mstsc.exe program to resources on the Internet.
Microsoft has provided indicators of compromise related to this campaign, as well as mitigations and hunting queries.