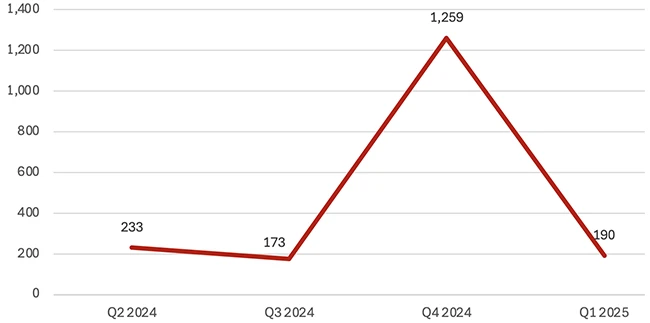
85% of phishing emails utilized malicious links in the content of the email, and spam emails increased by 30% from Q1 to Q2 2023, according to a VIPRE report.
Information technology organizations also overtook financial institutions (9%) as the most targeted sector for phishing in Q2 as compared to VIPRE’s previous quarterly report.
New macro-less malspam email campaign
- 58% of malicious emails utilized spoof content
- 67% of spam emails in Q2 originated in the US
- Qakbot was the top malware family in Q2 2023
In its analysis, VIPRE also discovered a new, macro-less malspam email campaign containing a spoof “.docx” – macro-less means the attacker bypasses the security warnings added to Microsoft Office programs in response to traditional macro malware. This specific campaign contained a malicious external resource page called up when the victim opened the file.
A previously unknown malspam email campaign exploits the CVE-2022-30190 (or “Follina) vulnerability, facilitating remote code execution (RCE) on the victim’s system by leveraging the Microsoft Support Diagnostic Tool (MSDT).
Furthermore, in Q2 2023, 58% (~130 million) of the nearly 230 million malicious emails VIPRE detected utilized nefarious content. Likewise, 42% (~95.7 million) of these emails involved malicious links, and, most interestingly, VIPRE detected 90,000 of the 5 million malicious attachments with behavioral-driven monitoring.
Malicious content
Malicious content likely tops the Q2 2023 list because, with security awareness programs becoming increasingly more common, users are less likely to open suspicious links or attachments. Cybercriminals use malicious content to trick victims into performing an action, such as approving or submitting a payment – significantly more challenging to detect.
The efficacy of malicious content also explains why so many scam emails (48%) in Q2 were BEC scams, as they typically favor content over links or attachments.
According to the report, the top email threat attack targets shifted significantly from Q1 to Q2 2023, with financial institutions falling dramatically from 25% in the first quarter to only 9% in quarter two. This decline is likely the result of financial institutions continuing to invest resources into preventing these attacks, which means a lower success rate by cybercriminals.
QR codes as key phishing attack vector
During the assessment, VIPRE also discovered that many phishing emails utilized QR codes as a primary attack method, which diverted users to a phishing page. The increased use of QR codes suggests that users are increasingly aware of traditional email-based attack techniques, such as malicious links or attachments, forcing threat actors to switch to more unconventional methods.
While most (67%) spam emails originate in the US, cybercriminals obfuscate their location of origin to avoid detection.
“Precious few vendors possess the experience, expertise, and resources to analyze the email threat landscape properly,” said Usman Choudhary, chief product and technology officer at VIPRE. “Based on the billions of data points available to us across a large and diverse set of our customers’ business environments, we’re able to utilize more than two decades of data and experience to deliver accurate and actionable email threat research.”