The latest variants of the P2Pinfect botnet are now focusing on infecting devices with 32-bit MIPS (Microprocessor without Interlocked Pipelined Stages) processors, such as routers and IoT devices.
Due to their efficiency and compact design, MIPS chips are prevalent in embedded systems like routers, residential gateways, and video game consoles.
P2Pinfect was discovered in July 2023 by Palo Alto Networks analysts (Unit 42) as a new Rust-based worm that targets Redis servers vulnerable to CVE-2022-0543.
Following its initial discovery, Cado Security analysts who examined P2Pinfect reported that it was abusing the Redis replication feature to spread, creating replicas of the infected instance.
Later, in September, Cado warned about spiking P2Pinfect botnet activity targeting systems in the United States, Germany, the UK, Japan, Singapore, Hong Kong, and China.
Today, Cado reports a new development concerning the botnet, which marks a significant evolution in the project’s targeting scope and ability to evade detection.
New MIPS variant
The latest attacks observed on Cado’s honeypots scan for SSH servers that use weak credentials and attempt to upload the MIPS binary via SFTP and SCP.
Interestingly, propagation for the MIPS variant isn’t restricted to SSH, as the researchers spotted attempts to run the Redis server on MIPS devices through an OpenWRT package named ‘redis-server.’
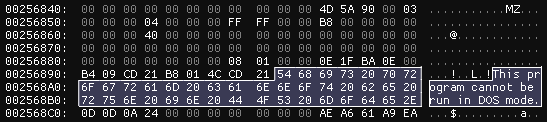
During static analysis, Cado researchers found that the new P2Pinfect is a 32-bit ELF binary with no debug information and an embedded 64-bit Windows DLL, which acts as a loadable module for Redis to enable shell command execution on the host.
More evasive
The newest variant of P2Pinfect implements sophisticated and multifaceted evasion mechanisms that make its detection and analysis much more challenging.
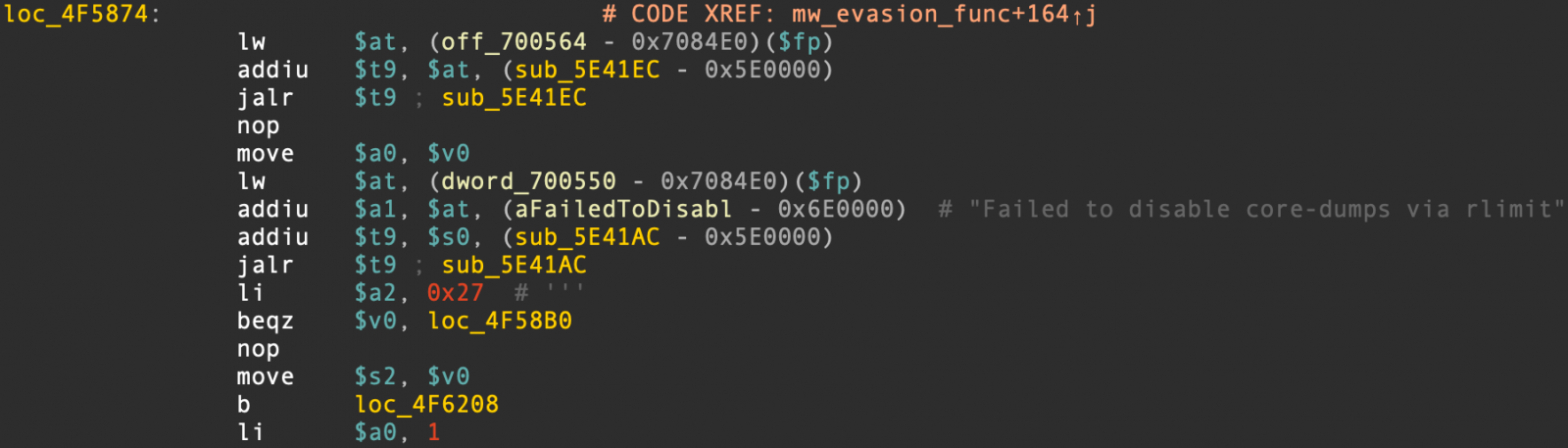
Cado has highlighted the following evasion mechanisms introduced in the latest P2Pinfect:
- Implementation of a check for the ‘TracerPid’ value in the process status file to determine if analysis tools are tracing the malware process, and terminating if it is.
- Usage of system calls to disable Linux core dumps, preventing the dumping of memory contents that contain traces of its activity.
- The embedded DLL contains a function for evading virtual machines (VMs)
The continuous development of P2Pinfect and expansion of the malware’s targeting indicates a high level of coding skills and determination from its authors.
It’s important to highlight that despite extensive tracking of the botnet through various campaigns over time, Cado Security remains uncertain about the precise objectives of the malware’s operators.
These goals could encompass cryptocurrency mining, launching Distributed Denial of Service (DDoS) attacks, facilitating traffic proxying, and executing data theft.