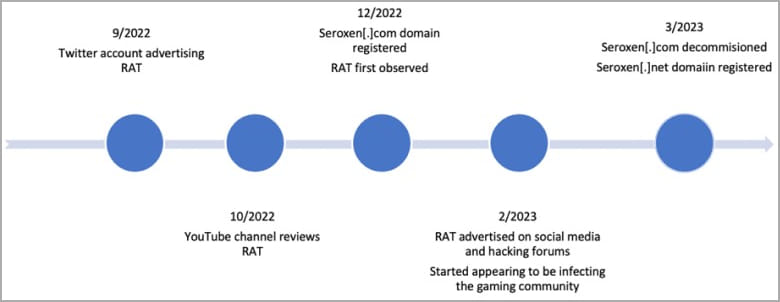
A stealthy remote access trojan (RAT) named ‘SeroXen’ has recently gained popularity as cybercriminals begin using it for its low detection rates and powerful capabilities.
AT&T reports that the malware is sold under the guise of a legitimate remote access tool for Windows 11 and 10 for $15/month or a single “lifetime” license payment of $60.
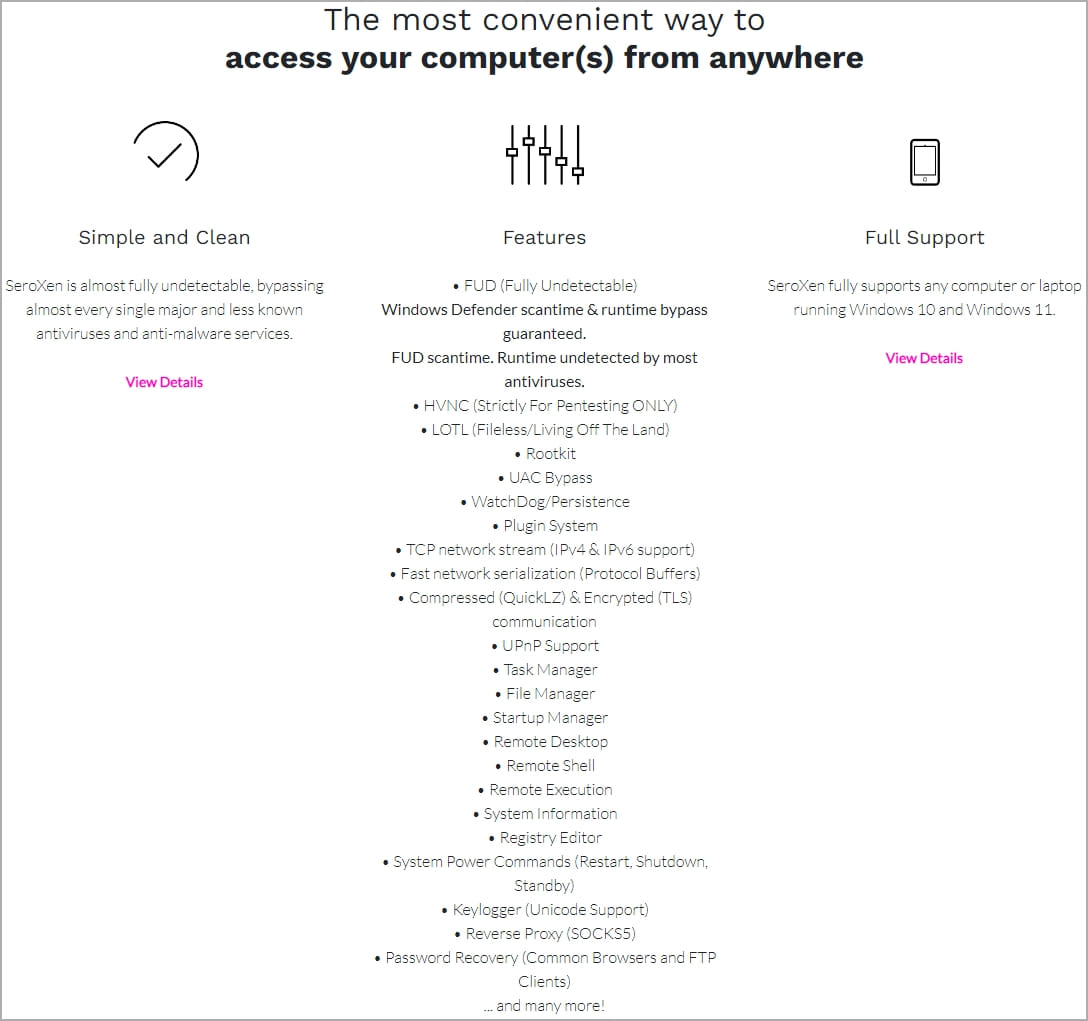
While marketed as a legitimate program, the Flare Systems cyber intel platform has shown that SeroXen is promoted as a remote access trojan on hacking forums. It is unclear if those promoting it on the forums are the developers or shady resellers.
However, the remote access program’s low cost makes it very accessible to threat actors, with AT&T observing hundreds of samples since its creation in September 2022, with the activity ramping up recently.
Most victims of SeroXen are in the gaming community, but as the popularity of the tool increases, the targeting scope could widen to include large companies and organizations.
Open-source building blocks
SeroXen is based on various open-source projects, including Quasar RAT, the r77 rootkit, and the NirCmd command line tool.
“The SeroXen developer has found a formidable combination of free resources to develop a hard to detect in static and dynamic analysis RAT,” comments AT&T in the report.
“The use of an elaborated open-source RAT like Quasar, with almost a decade since its first appearance, makes an advantageous foundation for the RAT […] while the combination of NirCMD and r77-rootkit are logical additions to the mix, since they make the tool more elusive and harder to detect.”
Quasar RAT, which SeroXen uses as its basis, is a lightweight remote administration tool first released in 2014. Its latest version, 1.41, features reverse proxy, remote shell, remote desktop, TLS communication, and a file management system, and is freely available through GitHub.
The r77 (Ring 3) rootkit is an open-source rootkit that offers file-less persistence, child process hooking, malware embedding, in-memory process injection, and antivirus evasion.
NirCmd is a freeware utility that performs simple Windows system and peripheral management tasks from the command line.
SeroXen attacks
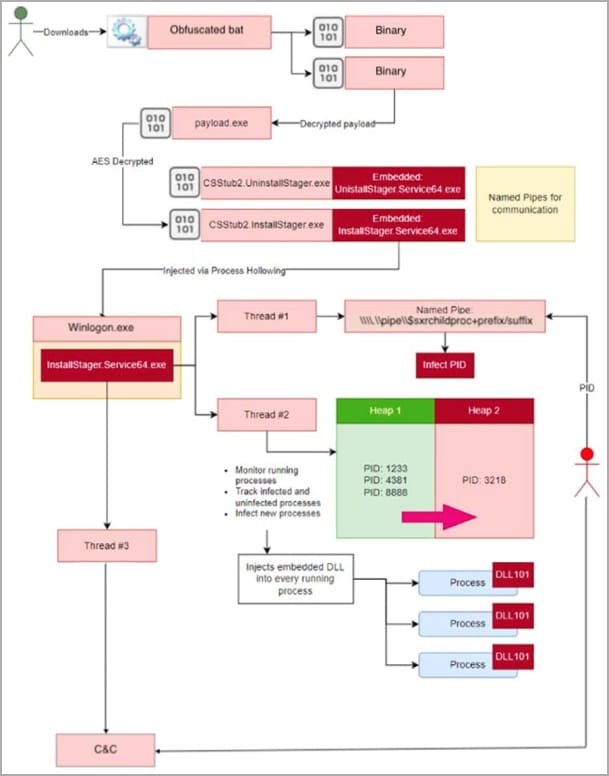
AT&T has seen attacks pushing SeroXen through phishing emails or Discord channels, where cybercriminals distribute ZIP archives that contain heavily obfuscated batch files.
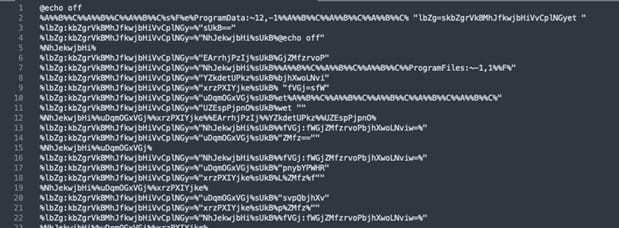
The batch file extracts two binaries from base64 encoded text and loads them into memory using .NET reflection.
The only file that touches the disk is a modified version of msconfig.exe, which is needed for the malware execution, and is temporarily stored in the short-lived “C:Windows System32” (notice the extra space) directory that is deleted once the program is installed.
This batch file ultimately deploys a payload named “InstallStager.exe,” a variant of the r77 rootkit.
The rootkit is stored in an obfuscated form in the Windows registry and is later activated using PowerShell via the Task Scheduler, injecting it into “winlogon.exe.”
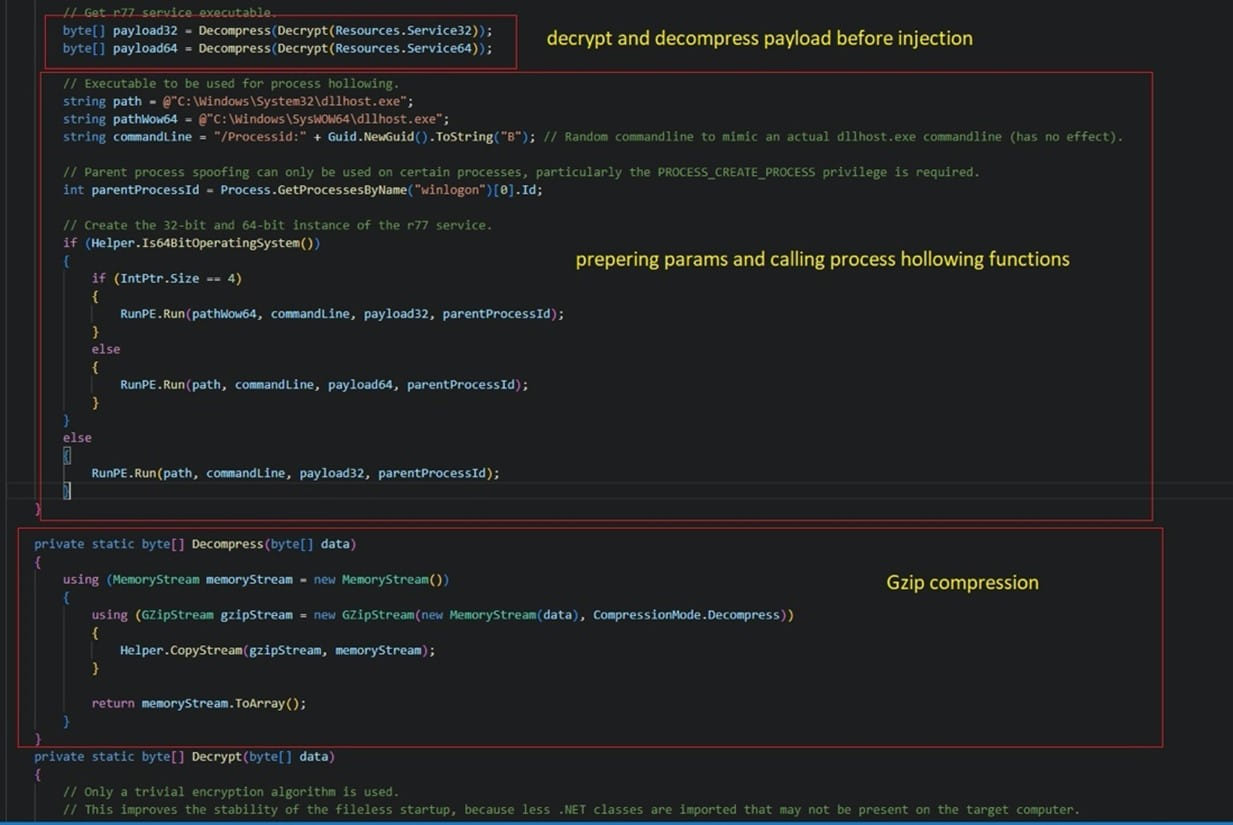
The r77 rootkit injects the SeroXen RAT into the system’s memory, ensuring it remains undetected and now providing remote access to the device.
Once the remote access malware is launched, it establishes communication with the command and control server and waits for commands issued by the attackers.
The analysts found that SeroXen uses the same TLS certificate as QuasarRAT and features most of the original project’s capabilities, including TCP network stream support, efficient network serialization, and QuickLZ compression.
AT&T fears that the growing popularity of SeroXen will attract hackers interested in targeting large organizations rather than focusing on gamers and has released indicators of compromise for use by network defenders.






