Will your organization fall apart if you don’t switch from a VPN to a zero trust network access (ZTNA) solution in the near future? I’m here to tell you it won’t.

The reality of VPN vs. ZTNA
For a while now, VPN has been the proven, go-to solution when thinking about the best way to provide secure connectivity and ensure safety of data in transit. In fact, many organizations today still use VPN when securing their workplace technology as they are more manageable and accessible than the newer technology. While this remains true, the cyber threat landscape has evolved and companies need stronger systems in place to keep data secure. According to a recent poll, 81% of respondents currently utilize VPN to support remote work and 87% of the respondents who still use VPN say they have implemented at least one other solution to close the gaps. Many organizations continue to use the VPN footprint while implementing another security solution, such as ZTNA, to ensure secure connectivity where VPN may not be able to.
For example, VPNs often allow lateral movement of threats. If a threat actor does break into a VPN-connected machine on an organization’s network, the VPN is a seven-lane highway that can be used to reach that organization’s crown jewels.
VPN remains a popular solution for supporting remote work, but security teams have come to realize that VPNs are complex to scale and often result in poor application performance. This can affect employee productivity and engagement and – in the case of a remote workforce – even morale. ZTNA can handle some of the toughest security challenges today. Additionally, organizations that have both ZTNA and VPN capabilities will be able to seamlessly add ZTNA for their users and easily transition their solution from VPN to ZTNA if they choose.
ZTNA also enables secure access and supports bring-your-own-device programs. The deployment of a zero-trust architecture allows an organization to provide secure access to its infrastructure and resources without connecting devices to a shared network – a must when it comes to both connecting with external partners and hybrid work. While some legacy systems give users access to all resources, ZTNA ensures that users are only given access to what they need, limiting the possibility of an insider threat. Given the sensitive information that employees have access to, it’s important that organizations have the strongest security possible to both limit the possibility of an attack and minimize the damage if one does occur.
Know thy risks
You may already be familiar and dealing with these and other challenges and might have even implemented some security measures to manage them. But you should know that using legacy solutions like VPN alone doesn’t continually authenticate the devices on your network and that a data breach on one of your devices could raise compliance issues with organizations like the General Data Protection Regulation (GDPR), which carries severe financial penalties. With many attacks coming from already authenticated users, it’s important to ensure that you’re using solutions that protect you from any and everything that may come your way.
This is where the addition of a ZTNA solution can help. For example, one of your employees’ laptops is running an outdated operating system, which puts your whole agency at risk. When a new OS is released, vendors often announce end-of-support or end-of-life for older products, leaving systems running with unpatched security vulnerabilities that make it easy for bad actors to launch cyberattacks. The burden is placed on the user, and unless they update their personal devices, these bad actors can wreak havoc. The 2017 WannaCry outbreak, for example, impacted over 160,000 outdated Windows machines.
In the case outlined above, because your employee did not update their OS version, the company is now vulnerable to attacks and data exposure. And once a device is infected with malware, it can propagate laterally from one device to another to eventually infiltrate your entire organization.
Be transparent
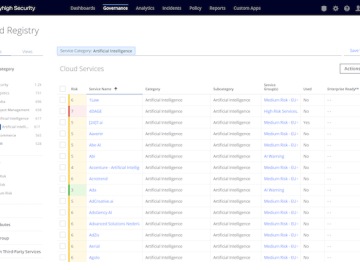
With the right security solution, you can make sure your organization is ready to stand against any threats, internal or external, that may arise. Before rushing to change your solution – it’s important you analyze any potential threats to choose the right solution for you. Commonly, organizations may choose to implement ZTNA for cloud migration, extending access to third-party users, providing remote access to employees, and even VPN replacement.
This concept of validating identity, context, and risk, and granting “just in time, just enough” access based on frequent evaluation of those metrics is the foundation of zero trust. And enforcing it requires two critical things:
- Deep understanding of the user and their device
- The ability to enforce granular controls on a per user, per session and per app level
IT and security teams must manage both in a transparent manner so as not to impact user experience or productivity. Regardless of where an employee is located and whether they’re using a company-issued or personal device, they need to be able to get work done in a simple, secure and reliable manner. In the same vein, IT needs an easy solution to set up, manage and scale to drive agility – something that is important when working to provide a seamless and accessible experience for employees.
If you choose to transition to ZTNA, it can be simple
It’s important to keep in mind that not all ZTNA solutions are created equal and an innovative approach to ZTNA begins at the browser. Enterprise-grade browsers that can enforce ZTNA for all browser-apps while delivering context-aware, uniquely granular, per app security policy are an upgrade from typical approaches as they are faster to deploy and offer more consistent and better user experiences, regardless of the user device.
The rapid move to modern applications and flexible work has created dynamic environments that are driving new levels of productivity and innovation – but the rewards are not without cyber risk. But as I said earlier, right now it’s not necessary to completely transition away from VPN immediately. By maintaining your VPN footprint and implementing a ZTNA solution and strategy, organizations can put themselves in the best position possible to respond to and defend against the growing number of threats that could hamper their success. It’s critical you work with a provider that offers hybrid solutions, so if you do choose one day to completely transition to ZTNA, it’ll be seamless.