Over the last several years, endpoints have played a crucial role in cyberattacks. While there are several steps organizations can take to help mitigate endpoint threats – such as knowing what devices are on a network (both on-premises and off-site), quarantining new or returning devices, scanning for threats and vulnerabilities, immediately applying critical patches, etc. – there is still much to be done to ensure endpoint security.
To achieve that, it’s important to understand some of the primary attack vectors hackers use against endpoints.
Phishing/spear-phishing
Phishing, especially spear-phishing, is an effective way for gaining access to endpoints to harvest user credentials.
It is not itself an exploit, but a method that threat actors use to deliver a payload – whether it’s a link to a fake Microsoft 365 web portal (for credential harvesting), or a macro-enabled word document with a malware payload that executes on opening.
Because of this nuance, it’s critical that security analysts implement not only email filtering (a crude defense, at best) but endpoint tools that would block the deployment of malware payloads delivered by email: antivirus (AV) and antimalware (AM). Implementing AV/AM products creates a safety net, blocking malware execution if a phishing email successfully bypasses corporate email filters.
We recently saw how threat actors deployed phishing to infect user endpoints at a massive scale with the IceXLoader malware. The malware is bundled into an innocent-looking ZIP file delivered as an email attachment. Once opened, the malware extracts itself to a hidden file directory on the C drive of an endpoint, providing a beachhead for the attacker to perform additional attacks to further breach the corporate network.
OS vulnerability exploitation
Vulnerabilities are made possible by bugs, which are errors in source code that cause a program to function unexpectedly, in a way that can be exploited by attackers. By themselves, bugs are not malicious, but they are gateways for threat actors to infiltrate organizations. These allow threat actors to access systems without needing to perform credential harvesting attacks and may open systems to further exploitation. Once they are within a system, they can introduce malware and tools to further access assets and credentials.
For attackers, vulnerability exploitation is a process of escalation, whether through privileges on a device or by pivoting from one endpoint to other assets. Every endpoint hardened against exploitation of vulnerabilities is a stumbling block for a threat actor trying to propagate malware in a corporate IT environment.
There are routine tasks and maintenance tools that allow organizations to prevent these vulnerabilities getting exploited by attackers. Patch management tools can scan devices, install patches (fixes), and provide reports on the success or failure of these actions. In addition, organizations can leverage configuration management tools to maintain OS configuration files in the desired secure state.
Software vulnerability exploitation
Software vulnerabilities exist in products (software) installed within an OS environment. For example, Google Chrome gets frequent patches from Google, primarily because it is a massive target for exploitation.
As with OS vulnerabilities, the best defense against exploits are the frequently released third-party patches/updates, the implementation of which can be facilitated by endpoint management tools.
Additionally, enforcing acceptable use policies can help reduce the opportunities for end users to engage in behaviors that could put their endpoints and company assets at risk.
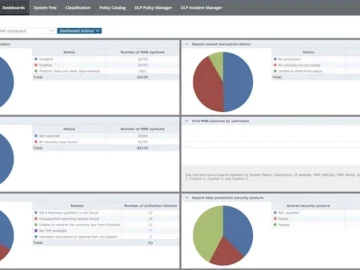
And beyond security information and event management (SIEM) and antivirus tools, organizations can drastically decrease the impact caused by a successfully executed ransomware attack by:
- Implementing data loss prevention (DLP) solutions
- Creating off-site backups
- Taking advantage of data storage solutions in the cloud
Conclusion
The changing cyberattack landscape requires IT and security departments to be nimble and evolve in tandem with threats. The fixes of yesterday may not work today – while the threats could be the same, their tactics are likely different. When working to mitigate network threats, do not forget the increasingly vital role endpoints play.