U.S. CISA adds Veeam Backup and Replication flaw to its Known Exploited Vulnerabilities catalog

U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Veeam Backup and Replication vulnerability to its Known Exploited Vulnerabilities catalog.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the Veeam Backup and Replication flaw CVE-2024-40711 (CVSS score of 9.8) to its Known Exploited Vulnerabilities (KEV) catalog.
This week, Sophos researchers warned that ransomware operators are exploiting the critical vulnerability CVE-2024-40711 in Veeam Backup & Replication to create rogue accounts and deploy malware.
In early September 2024, Veeam released security updates to address multiple vulnerabilities impacting its products, the company fixed 18 high and critical severity flaws in Veeam Backup & Replication, Service Provider Console, and One.
The most severe flaw included in the September 2024 security bulletin is the critical, remote code execution (RCE) vulnerability CVE-2024-40711 (CVSS v3.1 score: 9.8) impacting Veeam Backup & Replication (VBR).
Veeam Backup & Replication is a comprehensive data protection and disaster recovery software developed by Veeam. It enables organizations to back up, restore, and replicate data across physical, virtual, and cloud environments.
“A vulnerability allowing unauthenticated remote code execution (RCE).” reads the advisory.
Florian Hauser, cybersecurity researcher at CODE WHITE Gmbh, reported this vulnerability.
The flaw impacts Veeam Backup & Replication 12.1.2.172 and all earlier version 12 builds.
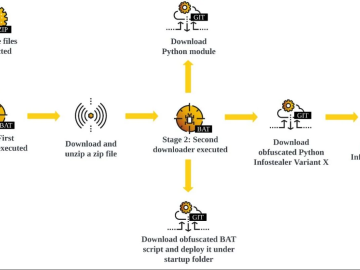
Sophos X-Ops researchers observed recent attacks exploiting compromised credentials and Veeam vulnerability CVE-2024-40711 to deploy ransomware, including Fog and Akira. Attackers accessed targets via VPN gateways lacking multifactor authentication, some of which ran outdated software. Overlapping indicators link these cases to prior Fog and Akira ransomware attacks.
“Sophos X-Ops MDR and Incident Response are tracking a series of attacks in the past month leveraging compromised credentials and a known vulnerability in Veeam (CVE-2024-40711) to create an account and attempt to deploy ransomware.” reads a statement published by Sophos on Mastodon.
“In one case, attackers dropped Fog ransomware. Another attack in the same timeframe attempted to deploy Akira ransomware. Indicators in all 4 cases overlap with earlier Akira and Fog ransomware attacks. In each of the cases, attackers initially accessed targets using compromised VPN gateways without multifactor authentication enabled. Some of these VPNs were running unsupported software versions.”
Threat actors exploited the Veeam URI /trigger on port 8000 to spawn net.exe and create a local account, named “point,” adding it to the local Administrators and Remote Desktop Users groups. In one case, the attackers deployed Fog ransomware on an unprotected Hyper-V server and used rclone for data exfiltration.
“These cases underline the importance of patching known vulnerabilities, updating/replacing out-of-support VPNs, and using multifactor authentication to control remote access. Sophos X-Ops continues to track this threat behavior.” concludes Sophos.
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix this vulnerability by November 7, 2024.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, CISA)