The Phoenix SecureCore UEFI firmware has discovered a new vulnerability, which runs on several Intel Core Desktop and mobile processors.
This vulnerability has been assigned CVE-2024-0762, and its severity has been given as 7.5 (High).
This was initially identified on Lenovo ThinkPad X1 Carbon 7th Gen and X1 Yoga 4th Gen, which uses the latest Lenovo BIOS updates, but later, Phoenix Technologies took responsibility to come forward and acknowledge the same issues exist on multiple versions of their multiple versions of SecureCore firmware.
UEFIcanhazbufferoverflow Flaw
According to the reports shared with Cyber Security News, this vulnerability exists on multiple Intel processor families and multiple generations of Intel core Processors, including AlderLake, CoffeeLake, CometLake, IceLake, JasperLake, KabyLake, MeteorLake, RaptorLake, RocketLake, and TigerLake.
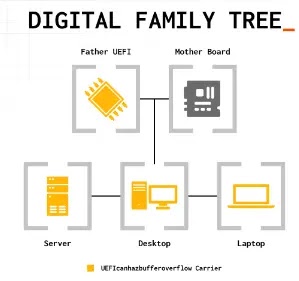
These processors are used by a wide range of OEMs (original equipment manufacturers) and ODMs (Original Design Manufacturers).
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot
Further, the same vulnerability also affects several vendors, affecting hundreds of PC products that rely on Phoenix SecureCore UEFI firmware.
However, this vulnerability allows a local threat actor to elevate their privileges and execute remote code within the UEFI firmware during runtime.
The vulnerability lies in the UEFI code handling TPM (Transform Platform Module) configuration, leading to buffer overflow and malicious code execution.
The possibility of exploiting this vulnerability depends on the configuration and permission assigned to the TCG2_CONFIGURATION variable, which is different on every platform.
Nevertheless, this vulnerability can be exploited similarly to firmware backdoors, which are widely used by threat actors.
If threat actors could exploit this vulnerability and plant a backdoor on vulnerable devices, it could enable them to evade security measures that run on the operating system and software layers.
Further, manipulating runtime code can also increase the difficulty of detecting these attacks.
Vulnerability Analysis
The module that has been identified as vulnerable was GUID: E6A7A1CE-5881-4B49-80BE-69C91811685C.
Two calls are made to GetVariable with the “TCG2_CONFIGURATION” argument and the same DataSize that does not have sufficient checks.
If a threat actor attacks the TCG2_CONFIGURATION by manipulating the value, it could allow them to set it to a value for longer periods.
Further, the first call to GetVariable returns EFI_BUFFER_TOO_SMALL, and the data_size is set to the length of the UEFI variable.
The second call allows them to overflow the buffer successfully, eventually leading to stack buffer overflow.
Users of these firmware versions are advised to upgrade their vendor-issued patches to patch this vulnerability.
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free





