What are web security trends for 2020? This year we anticipate the build-up of a new security market category, growing targets in automation, a new perimeter and continuation of DevSecOps. Here is what we are watching for in 2020:
We’ve added a part 2, featuring insights from security leaders.
Rise of the “Crowdsourced Security” market
Keeping up with the threat landscape is a common pain point for many developer teams and C-level personnel. In fact, 48% of developers in this survey know security is important but don’t have enough time to spend on it. Even with a good overview of your software asset inventory, the digitalization of companies requires modern and automated ways of working with security, which is why more are adopting Crowdsourced security. This means they are gathering security knowledge from external experts – ethical hackers and bug bounty hunters. This is the principle behind Detectify Crowdsource.
Crowdsourced security is an up-and-coming industry and MarketsandMarkets reported that it will grow up to USD 135 million by 2024. Bug bounty programs could be the first thing that comes to mind, but there are other companies in this space offering options that don’t require top-dollar. For example, Detectify collaborates with ethical hackers to make the knowledge available through automation to users with or without a crowdsources security program.
As mentioned in the Undetected podcast, some hackers report with goodwill, which is why setting up a responsible disclosure policy is a good way to begin working with ethical hackers, and we even saw examples of such vigilance in the recent case of Citrix, where malicious hackers exploited it wildly for personal gain, while this report suggests there could be a vigilante that’s using it in a way to beat others to the punch. It would have been a challenge for Citrix to thoroughly communicate the issue to all their users at once, and with the reach of ethical hackers, the information has probably gotten to some companies sooner. For this reason, we anticipate more companies to add Crowdsourced security services to their toolbox.
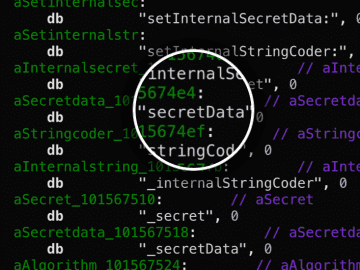
CI/CD automation becoming the low hanging fruit
Today, the low-hanging fruit is rarely finding a SQL injection in a website, but the attackers are starting to look elsewhere for easy access into sensitive information and internal servers – the automation process.
Taking into consideration the increasing CI/CD processes and tools, there are attack surfaces that, while not new, have become more critical. This means misconfigurations, the tools, and dependencies used for deployment and orchestration, or a storage place of API tokens for integrations, are increasingly interesting for attackers.

Misconfigurations, especially when CI/CD tools are used in cloud environments, can accidentally leave internal data storage exposed online due to lack of authentication or general security as in this case with MongoDB. While some of these can be caused by manual error, automation certainly doesn’t make it easy to evaluate the perimeter of your cloud environment. Accidentally exposing internal services or data to the public Internet seems to be a growing trend throughout 2019 and is expected to keep on growing in 2020.
Sometimes attackers dig deeper even beyond the code stored in your private code repositories. They go after the dependencies. This makes sense, because how often does an average organization review the source code for a Dockerfile that uses public images from Dockerhub? Running automated security in the background can help identify common security bugs and schedule fixes into the development cycle.
Cloud-powered web apps become the perimeter to defend
Nothing in the cloud is inherently secure or insecure. Cloud service providers employ a shared responsibility model, which roughly means that it is the user’s responsibility what and how the user deploys on the cloud provider’s service. The majority of improper access controls happen through misused credentials or API tokens, or misconfigurations in the services used, such as setting 0.0.0.0/0 firewall rules and allowing all access to internal data storage.
The sense of perimeter is different in cloud services (or at least some of them), because they introduce networking on the software level and in addition to IP addresses, some resources may have resource names and URLs that can be queried. The “Great Firewall” solution cannot be replicated in cloud environments, when access rights need to be given and blocked on the instance level, or with role-based access control solutions. Also, every cloud provider comes with different default configurations– some cloud providers may not deny traffic by default or may not force to generate strong passwords for data storage.
New web apps are stretching the security perimeter each time, and companies that can scale security with development will keep up with the rate at which vulnerabilities are discovered and exploited. Not only do companies need to monitor the security of their own code, but it’s important to also check for security when acquiring 3rd party software tools and javascript. You may already spend a large portion of your budget securing your main application, and keeping track of the growing inventory of web applications will need just as much attention.
DevOps continues towards DevSecOps
External tools and sources for testing for misconfigurations, many of the cloud service providers offer a wide variety of services and tools to support security. However, as stated above, the way these services are used and the type of security controls implemented is up to the developers building things in the cloud. Cultivating security culture amongst developers and taking advantage of available security assessing tools can make a difference in any environment.
The web is becoming safer due to improved frameworks used in web development, regulations around data security and increased know-how of developers. They’re doing this by considering security earlier in the software development lifecycle. There’s a lot of talk about shifting left or pushing left, and for good reason. Developers in advanced tech organizations are practicing DevOps and see the importance of including security as part of their role, and (surprise!) the security bit isn’t slowing them down. Just take a look at companies like Netflix, Atlassian, Slack – they are often speakers for better app security at OWASP AppSec conferences and more. Security becomes enabling, and is scaled up together with development. This isn’t a new trend, but we expect it to continue to grow.
Make it a safer 2020
There is no silver bullet to security, and it is ultimately a sum of many things including threat-modeling, pen-testing, automated security, asset monitoring, etc. Leaders in SaaS and tech use a combination of Crowdsourced security, CI/CD practices, cloud-native solutions and a positive security culture like DevSecOps, which is why we are keeping an eye on these areas for 2020. We’ve added a part 2, featuring insights from security leaders.
How can Detectify help with web security trends of 2020?
Detectify is the first company of its kind to automate the cutting-edge knowledge of the best ethical hackers in the world to secure public web applications. Users check web applications against 1500+ known vulnerabilities beyond the OWASP Top 10. In a fast-paced tech environment, the potential attack surface increases with each release and new app created. Using Detectify, you can monitor your subdomains for potential takeovers and remediate security issues in staging and production, and find vulnerabilities as soon as they are known, to stay on top of threats. Keep up with web security trends in 2020 with Detectify. Get a guided demo or try Detectify on your own with a 14-day free trial.
Written by: Laura Kankaala, Security Researcher
Edited by: Jocelyn Chan, Content Manager