LockBit ransomware gang offered a free decryptor after the attack on Canada’s largest children’s hospital based in Toronto. The group also issued an apology for the incident.
On its leak site, the group claimed that the ‘partner’ who violated their internal affiliate program had been removed from the network. As per reports, the group apparently has a noble policy of not attacking hospital groups.
“We formally apologize for the attack on sikkids.ca and give back the decryptor for free, the partner who attacked this hospital violated our rules, is blocked and is no longer in our affiliate program,” read the post.
While LockBit clearly indicated their intentions and approach in terms of attacks on healthcare sector this year, Hive ransomware group, on the other hand, added Spanish healthcare provider Centro Médico Virgen De La Caridad to its victim list.
Both incidents happened hours apart on the New Year. As one took a back step from the healthcare sector, the other set forth on the trail of cyberattacks focusing on healthcare.
Although, several healthcare institutes have been subjected to cyberattacks over the past few days during the weekend. It is not common for cybercriminals to resort to apologies and offer free decryptors, which are usually bartered with the intent of demanding ransom.
The growing list of hospitals attacked by ransomware
The Hive ransomware group encrypted the systems of Cartagena, Spain-based hospital Centro Médico Virgen De La Caridad on 21st December 2022. On January 1, ElderPlan, which is a New York-based non-profit medicare providing facility, was targeted. The threat actor group claimed to have leaked the healthcare data of over 44,745 patients.
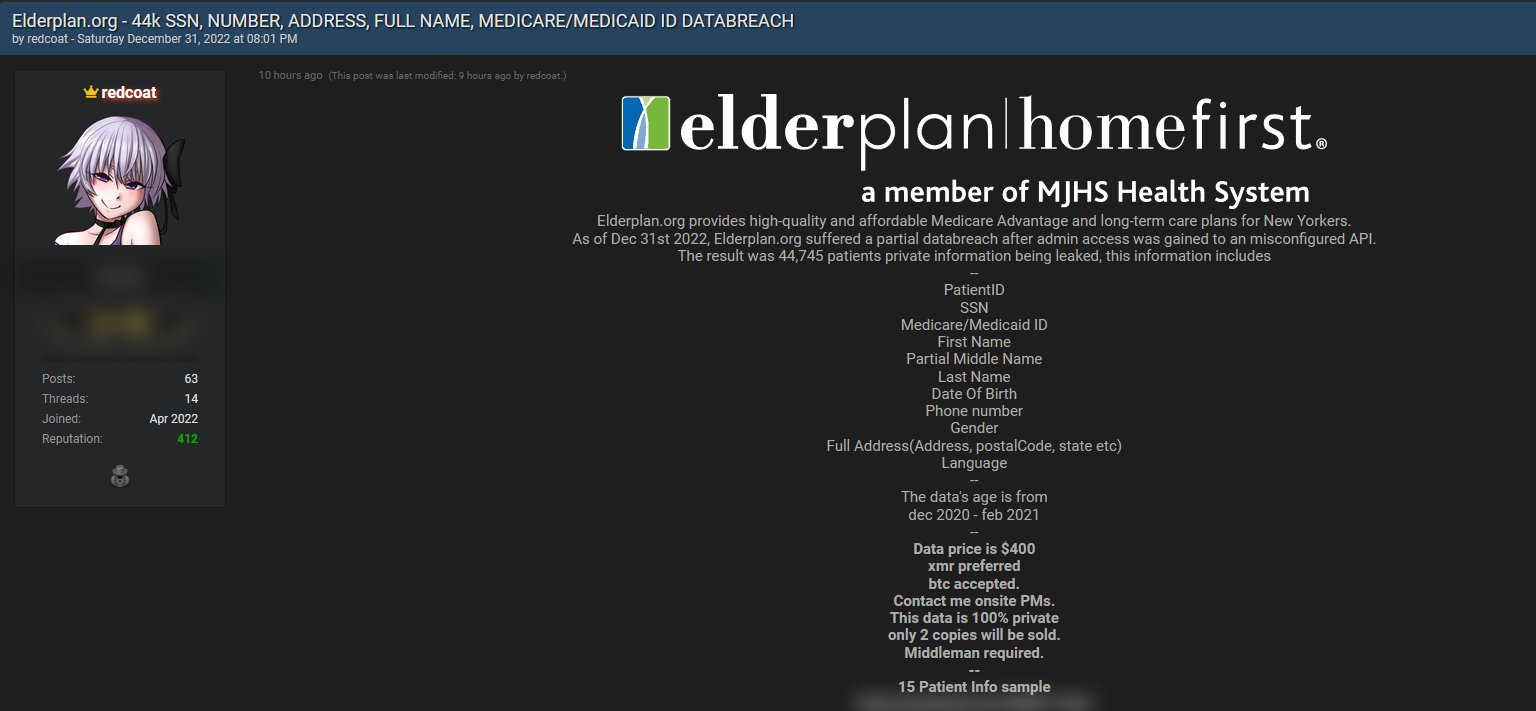
The post claimed to have kept the data 100% private and demanded a ransom of $400 followed by seeking payment in Monero (XMR) cryptocurrency.
SickKids’ response to the apology
While SickKids was announcing the improving condition of malnourished children on December 19, it had to deal with severed network systems after the ransomware attack hit the same day. The hospital activated the incident management command center to prevent further damage to its systems.
On December 22 it notified and speculated that the systems may remain offline for a ‘prolonged time,’ while assuring that patient care was largely unaffected by the ‘code grey’ condition.
Code grey in healthcare alerts the staff about the loss of necessary utilities like telecommunications. On December 29, the healthcare provider announced that nearly 50% of the systems were restored. As of January 2, the hospital is still experiencing connection issues on some of its websites related to early mental health promotion and specialty food.
Reacting to the announcement of the free decryptor made available by LockBit to the healthcare, the hospital posted on its website that it is aware of the news and the investigators are looking into its authenticity. No further updates have been shared by the facility.