It’s a common story: weak or reused passwords find their way online, with damaging consequences for organization. Criminals increasingly deploy stolen credentials to gain initial access to user accounts, bringing new demands for security.
This had led to a booming market for stolen credentials and the initial access they can bring. The ENISA Threat Landscape 2023 report said there had been year-over-year growth in the Initial Access Broker (IAB) market, with credentials the prime goods for sale.
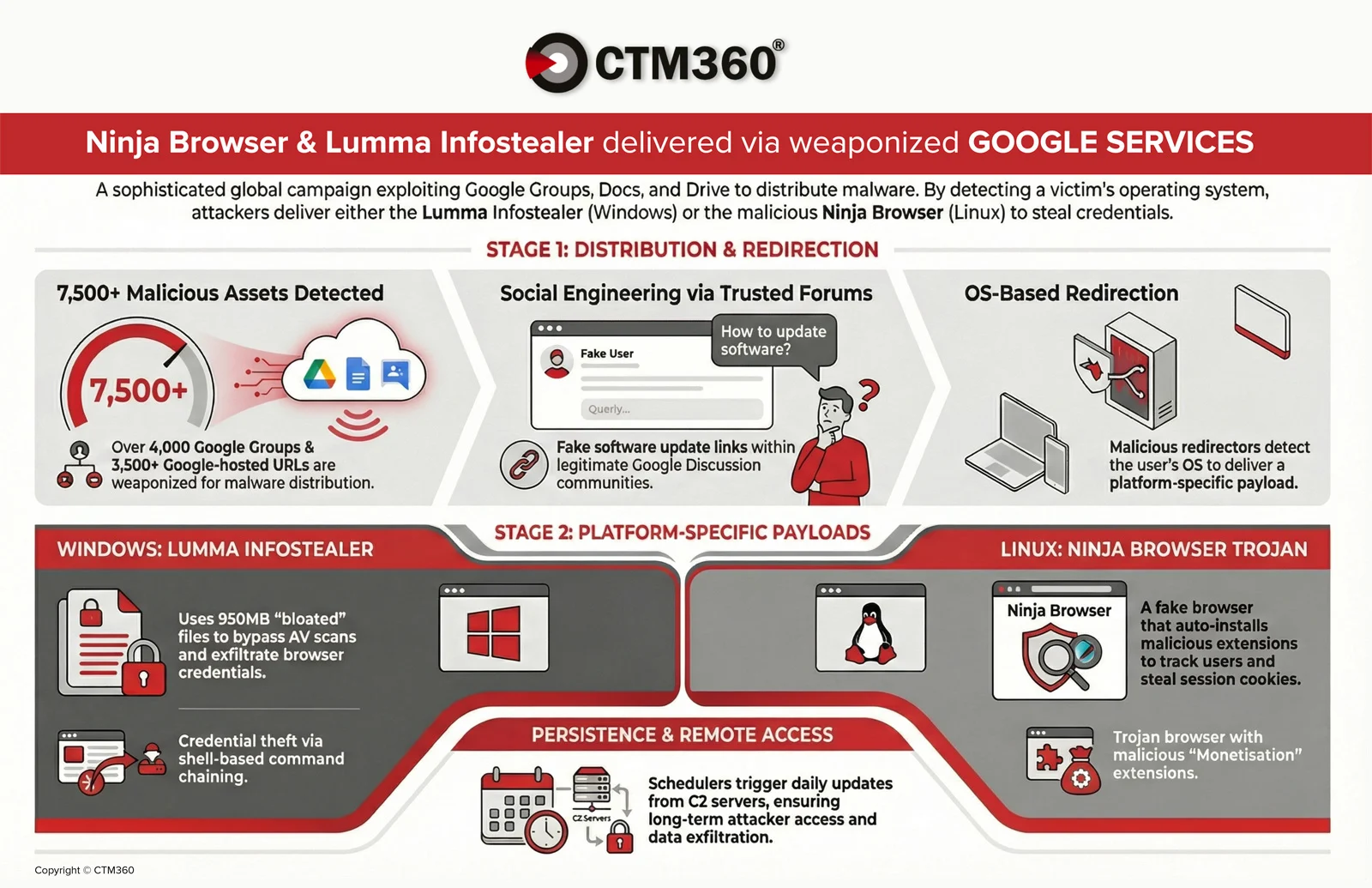
Stealer malware ‘commonly find their way to victim machines via social engineering, mostly phishing, some even via a paid distribution scheme relying on the Emotet and Qakbot botnets,’ ENISA wrote. ‘Other campaigns lure users into downloading seemingly legitimate software, for example via malvertising.
We expect that future social engineering campaigns to obtain credentials and install information stealers will further anticipate new defensive measures to protect the abuse of credentials.’
Stolen credentials are a bigger problem than ever
Challenges for organizations around stolen credentials are only getting bigger. The Verizon 2024 Data Breach Investigation Report (DBIR) found that attacks that involved the exploitation of vulnerabilities as the critical path to initiate a breach had increased by 180% compared to the previous year.
They found the use of stolen credentials to be the top initial action in breaches at 24%, just ahead of ransomware on 23%.
The threat is pervasive, with fraudsters using various means to steal credentials. One common ploy is to use malware to steal passwords and then sell them on the dark web, with such tools as Redline, Vidar, and Raccoon Stealer being popular choices.
The FBI has warned of cyber criminals using search engine advertisement services to impersonate brands and direct users to malicious sites that host ransomware to steal login credentials.
Credentials can also be guessed through approaches like brute force attacks, where cybercriminals deploy tools that test password combinations continuously until they discover the right one.
This can involve a range of methods, from relatively simplistic trial and error approaches to dictionary attacks, which exploit users’ habits of choosing simple and easily remembered passwords by attempting all the words in a “dictionary” of common passwords.
Potential for major breaches
Perhaps the most infamous recent breach and cyberattack was the Solarwinds attack, a sophisticated supply chain attack on the company’s Orion platform that Microsoft Corp President Brad Smith labelled “the largest and most sophisticated attack the world has ever seen”.
A compromised SolarWinds password was discovered existing on a private Github repository from June 2018 to November 2019; an intern for SolarWinds had set the password solarwinds123 on an account that was granted access to the company’s update server.
There are numerous other examples that highlight the potential danger. For example, consider the Dropbox breach, which impacted millions of users.
This saw a Dropbox employee reuse a password that had itself been part of a breach on LinkedIn, where millions of passwords were accessed by thieves.
As the ENISA report notes, the abuse of valid accounts for initial access is ‘not a novel technique’ but remains a successful focus for cybercrime actors. Misconfigured accounts were especially notable, it said – as were accounts with weak passwords.
And while multi-factor authentication (MFA) stops a lot of these attacks, it isn’t bulletproof, with ENISA pointing to actors intercepting MFA codes, harassing users with push notifications, and more.
“We expect that credentials [will] remain a focal point for cybercrime actors,” ENISA said. “Despite technical protective measures, cybercrime actors have found ways around them.”
Reduce the risk of initial access through stolen credentials
Cybersecurity experts will be fully aware of the danger of stolen credentials and the need for the strongest possible security. But there’s no room for complacency. The initial access threat posed by stolen credentials is evolving all the time – and so must we.
At the most basic level, you have no idea what your end users – your colleagues, for example, or your customers – are doing online, or where they are reusing their weak passwords. You cannot know the websites they use and the devices they deploy.
It’s also vital to enforce the creation of stronger passwords that are resistant to brute force techniques and other forms of attack.
Specops Password Policy helps build a robust password policy by:
- Generating personalized dictionary lists to prevent the use of commonly used words within your company.
- Giving immediate and interactive updates to users when changing passwords.
- Restricting the use of usernames, display names, certain words, consecutive characters, incremental passwords, and repeating parts of previous passwords.
- Applying this feature to any GPO level, computer, individual user, or group within your organization.
- Continuously scanning for and blocking more than 4 billion compromised passwords. (With its continuous scan feature, it can ensure that breached passwords are found daily, a vital advantage in the battle against an ever-evolving foe.)
Increasing the overall password security in the environment, enforcing good password hygiene, and eliminating breached, incremental, and otherwise weak passwords help to bolster the security of your Active Directory environment and privileged accounts.
But do you even know the password hygiene of your Active Directory? Better prepare your defenses by scanning for password vulnerabilities in your Active Directory, enabling you to detect weak and compromised passwords.
Download Specops Password Auditor for free and get a read-only report.
Sponsored and written by Specops Software.