Threat actors are increasingly weaponizing trusted administrative software to bypass security defenses.
By exploiting legitimate software, cybercriminals gain persistent, hands-on-keyboard (HOK) access while hiding within normal network activity.
Initial Access and Attack Methods
RMM compromises typically begin with targeted social engineering and phishing campaigns.
Attackers trick employees into downloading a malicious RMM agent disguised as routine business files, granting the attacker immediate access without triggering endpoint detection and response (EDR) alerts.
Since the RMM binary is a valid administrative tool, it does not appear malicious to traditional security systems looking for known bad signatures like ransomware or remote access trojans.
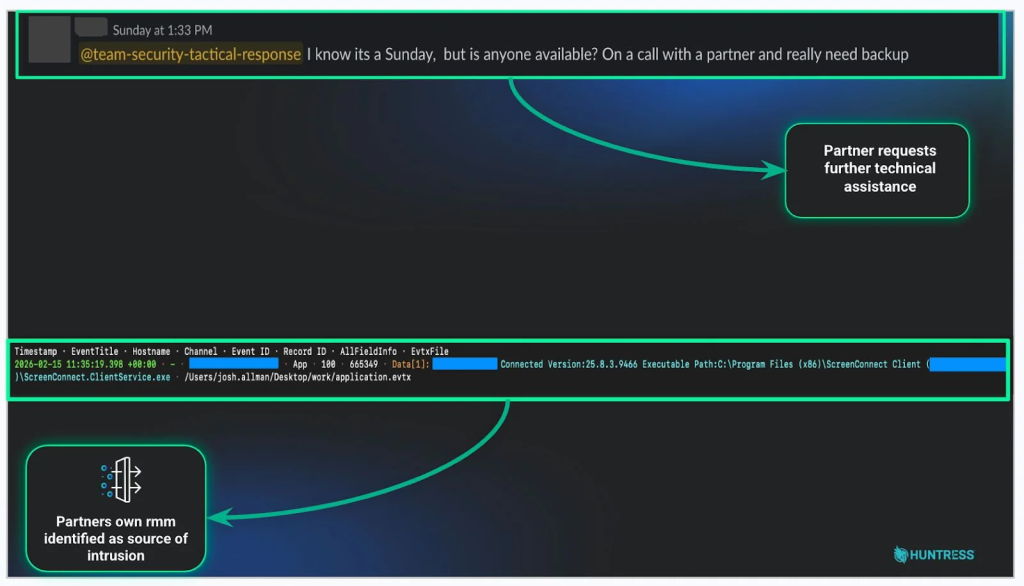
According to the Huntress 2026 Cyber Threat Report, analyzed by Beth Robinson, the abuse of Remote Monitoring and Management (RMM) tools surged by an alarming 277% in 2025.
Once inside, adversaries use these trusted tools to move laterally, automate tasks, and deploy destructive payloads rather than writing custom malware from scratch.
When attackers compromise an RMM solution managed by a Managed Service Provider (MSP), they can immediately access multiple downstream customers in a massive supply chain attack.
The Huntress report notes that over 50% of incidents involving suspicious Atera RMM activity are directly linked to ransomware, which can unfold and execute in as little as an hour.
In 2025, attackers relied heavily on specific phishing lures to deploy these agents:
- E-signature requests (14.2%): Disguised document links seamlessly install an RMM agent in the background.
- Invoice notifications (7.8%): Fake billing documents prompt the user to authorize malicious downloads.
- Voicemail notifications (7.5%): Audio alerts redirect victims to attacker-controlled payloads.
- File shares (6.8%): Bogus shared drive links grant immediate environment access upon clicking.
Defense and Mitigation Strategies
To combat this growing threat, organizations must shift from simply trusting approved software to actively verifying user behavior.
Security teams should define a strict baseline of normal IT operations to identify anomalies, such as unexpected script execution at unusual hours.
If a tool is authorized but behaves irregularly, it warrants immediate investigation before it escalates into data exfiltration.
A proactive defense requires continuous fingerprinting of the digital environment. IT administrators must track approved RMM executable hashes, monitor specific connection URLs, and treat any unverified remote access tool as a potential intrusion.
By maintaining a strict inventory and explicit allowlist, security teams can rapidly block unapproved RMM variants and connections to unknown servers.
Finally, the human element remains a critical defense layer against these deceptive tactics. Implementing comprehensive Security Awareness Training (SAT) teaches staff to spot sneaky phishing and social engineering attempts before granting access.
Fostering a “see something, say something” culture ensures that suspicious behavior is reported and investigated immediately, closing the dangerous gap between initial infection and detection.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.