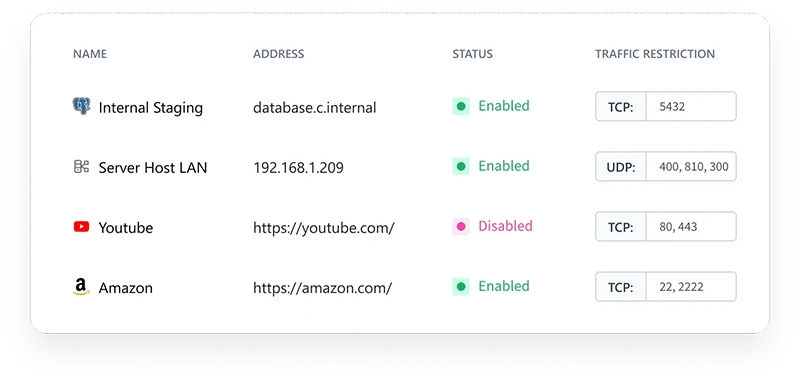
Wireless vulnerabilities are being disclosed at a rate that has no precedent in the fifteen-year history of systematic tracking. In 2025, researchers published 937 new wireless-related CVEs, an average of 2.5 per day, according to a threat report from Bastille Networks based on data from the NIST National Vulnerability Database.
Wireless threats increasing 20X faster than overall CVE disclosures (Source: Bastille Networks)
Wireless CVEs are growing 20 times faster than the broader CVE field
The wireless CVE category has expanded from 4 disclosures in 2010 to 932 in 2025, a 230× increase. When indexed against the same 2010 baseline, wireless disclosures have grown at more than 20 times the rate of total CVE disclosures across all technology categories. Wireless CVEs now account for nearly 2% of all annual disclosures.
Annual growth rates for wireless CVEs have exceeded 25% in every year since 2016, with the exception of 2023, which came in at 18%. The peak was 56% in 2017. The cumulative total has doubled every two to four years since 2014.
Industry forecasts project that total annual CVE disclosures across all technology domains will exceed 50,000, reflecting accelerating discovery and reporting activity across software, firmware, and embedded systems. Wireless disclosures are part of that broader surge, and the Bastille data indicates they are growing faster than the overall field.
Wi-Fi and Bluetooth account for most of the volume
Wi-Fi is the dominant contributor to wireless CVE counts. By 2025, Wi-Fi accounts for roughly 60% or more of wireless disclosures. Bluetooth is the second-largest category and has shown multiple surge years since 2016. Its prevalence across mobile, medical, automotive, and IoT devices makes its growth operationally significant.
Cellular vulnerabilities, covering LTE and 5G, remain lower in raw count. The report notes these figures may be structurally underreported given the complexity of baseband processors and the opacity of carrier firmware. Zigbee disclosures remain a small fraction of the total, appearing consistently each year across embedded and building automation contexts.
Notable disclosures span chipsets and protocols
Several high-profile vulnerabilities disclosed in 2025 illustrate the systemic nature of wireless exposure.
WhisperPair, tracked as CVE-2025-36911, is a Bluetooth flaw that allows an attacker to force wireless audio accessories to pair without user interaction. Any Bluetooth-capable device within approximately 14 meters can initiate pairing in seconds. Once paired, an attacker gains control of the audio device, including access to the microphone. The vulnerability affects products from multiple major manufacturers.
In the Wi-Fi category, researchers disclosed memory corruption flaws in MediaTek WLAN drivers, tracked as CVE-2025-20631, 20632, and 20633. The vulnerabilities exist at the driver level and can enable privilege escalation and, in some configurations, remote code execution, with no user interaction required once a device is within wireless range. MediaTek drivers are embedded in a broad range of consumer and enterprise devices.
CVE-2025-20753 affects MediaTek 5G modem firmware across NR15 and NR16 platforms and several Dimensity and IoT chipsets. An uncaught exception in the modem firmware can be triggered when a device connects to a rogue base station, causing the modem to crash and disrupting connectivity. No user interaction or additional privileges are required.
CVE-2025-1221 affects Zigbee Radio Co-Processors running the Silicon Labs EmberZNet stack. Under heavy traffic, the co-processor may fail to forward messages to the host controller and become unresponsive until hard-reset. The flaw can disrupt Zigbee-based mesh networks, which are common in building automation and operational environments.
Patching constraints extend exposure windows
A structural feature of wireless CVE risk is that many affected devices cannot be patched or receive firmware updates on standard enterprise timelines. IoT sensors, SCADA equipment, and embedded industrial controllers often have no mechanism for centralized patch management. Zigbee and cellular devices may depend on vendor-issued firmware releases that arrive slowly or never.
This means disclosed vulnerabilities accumulate in deployed environments. Each year’s disclosures add to a base of existing, unresolved exposures. The longer a device remains in service after a vulnerability is published, the larger the window for exploitation.
AI-assisted attacks are an emerging factor
Attackers are expected to increasingly use machine learning to scan wireless environments and identify targets. Models trained on RF telemetry and device fingerprints can help prioritize environments with dense Bluetooth peripheral usage or exposed Wi-Fi infrastructure.
Generative AI tools can assist in adapting publicly disclosed vulnerability details into usable attack workflows. Automated tooling can scan for nearby wireless activity, attempt opportunistic pairing or protocol interaction, and adjust based on device responses.
Nation-state actors are likely to integrate AI-driven analytics with custom wireless tooling for persistent reconnaissance against government facilities, defense contractors, and critical infrastructure. Wireless protocols offer access paths that bypass traditional network defenses and intersect with operational systems that are difficult to update.
The visibility gap
Traditional vulnerability management relies on asset inventories, authenticated scanning, and patch tracking. Those controls do not reliably detect personal Bluetooth peripherals, embedded Zigbee systems, transient third-party wireless equipment, or cellular-connected devices operating outside enterprise network boundaries.
Bastille recommends continuous passive monitoring of the wireless radio frequency environment as a near-term measure to gain visibility into non-IP wireless devices. Over the medium term, the recommendation is to integrate wireless data into existing vulnerability management and incident response workflows. Strategically, the report calls for extending wireless visibility beyond Wi-Fi and Bluetooth to cover Zigbee, LTE, and 5G.
“We’ve long said that wireless threats are proliferating, and this report illustrates the alarming extent to which that is the case as well as highlights the theft and espionage risks companies and governments face,” said Chris Risley, CEO at Bastille Networks. “Anything that can be controlled wirelessly is vulnerable. With the explosion of new AI data centers and other high-value targets worth billions of dollars in intellectual property or trade secrets, now is the time for enterprises to start treating wireless visibility and vulnerability management as foundational security infrastructure.”
If current growth rates persist, annual wireless CVE disclosures will exceed 1,500 within the next several years.
![]()
Webinar: The True State of Security 2026