AvosLocker ransomware gang has attacked United Kingdom’s Children Health and Care Specialist Cambian Group.
The UK’s children specialist operates a network of hospitals, schools, and homes for children and adults with learning disabilities, autism, and mental health conditions.
Avos Locker posts the United Kingdom’s leading specialist behavioral health and care services for children.
/cambiangroup.com#cybersecurity #infosec #AvosLocker pic.twitter.com/0FGllSHTTI
— Dominic Alvieri (@AlvieriD) January 9, 2023
The company was founded in 2002 and is headquartered in Altrincham, Greater Manchester, England.
AvosLocker attacks organizations in different domains
AvosLocker is a relatively new type of ransomware that has emerged in recent years, taking the place of previously prominent strains like REvil. While it may not be as well-known or widely active as other threats like LockBit or Conti, it is steadily gaining attention, with the FBI issuing an advisory about it.
According to the advisory, AvosLocker has targeted critical infrastructure in industries within the US and other countries like Canada, the UK, and Spain. Although this ransomware is not widespread, its use of proven tactics makes it worth keeping an eye on.
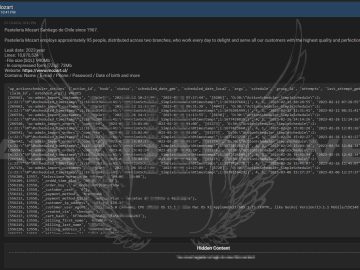
The Cyber Express found two more instances of AvosLocker wherein the threat actor targeted Corporate Interiors Inc on 2023-01-07, Cambian Group, and Arizona Labor Force on 2023-01-09.
How AvosLocker works?
The site instructs the victim to pay the ransom to retrieve the decryption key to decrypt the application or files. The victim submits their payment via a “payment page.” If the payment is not made, their data goes up for sale. Also, an affiliate program is also offered by AvosLocker.
AvosLocker is an emerging threat in the form of a ransomware-as-a-service (RaaS) model, it first appeared in the threat landscape in July 2021 and since then several variations have been observed. AvosLocker is known for the following key features:
It uses the remote administration tools
AvosLocker campaigns are known for their utilization of AnyDesk, a remote administration tool that enables the operator to access and infect victim machines. This tool allows the attackers to manually control the compromised device and perform various malicious actions.
It runs in safe mode
One of AvosLocker’s key evasion techniques is its utilization of safe mode. By restarting the affected machine and disabling certain drivers, the malware is able to evade detection by security measures that cannot function in this mode.
Additionally, the attackers have set up specific drivers that allow the malware to continue running even in safe mode. This tactic was also employed by its predecessor, the now-defunct REvil malware.
Feeding off the operator’s auction
AvosLocker has taken inspiration from REvil’s tactics by adding a new dimension to their operation – auctioning off the stolen data on their website and their traditional double extortion scheme. This could be viewed as a way for the group to not only monetize a successful attack even further but also to recoup losses from a failed one.