A cybercriminal collective, known as Cloak, has confirmed its involvement in an attack targeting the Virginia attorney general’s office in February 2025. This attack has reportedly caused disruption, compelling officials to enact emergency measures.
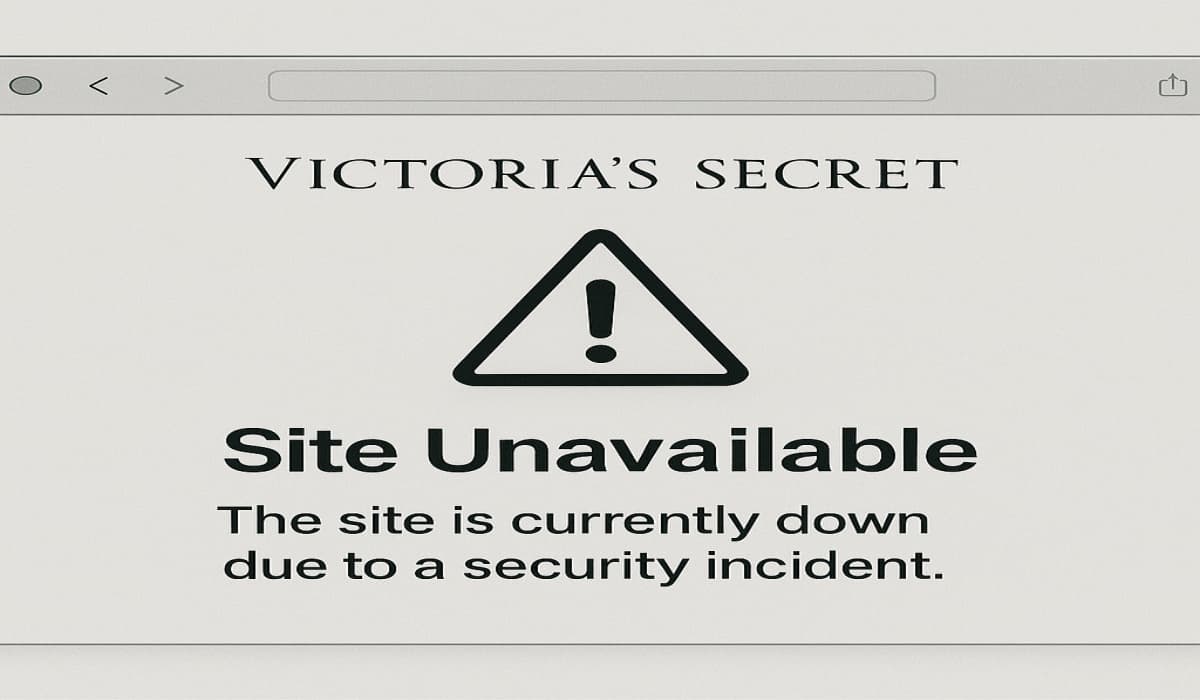
Chief Deputy Attorney General Steven Popps communicated to staff via email that the majority of the office’s IT resources, which included vital systems such as email, virtual private network access, internet connectivity, and the attorney general’s website were rendered inoperative, as reported by the Washington Post.
The disruption also forced employees to revert to traditional paper-based documentation processes. In response, the attorney general’s office promptly notified the Virginia State Police, the Federal Bureau of Investigation (FBI), and the Virginia Information Technologies Agency, and investigations were initiated into the incident.
On 20 March, Cloak publicly listed the Virginia attorney general’s website on their Tor-based data leak platform, accompanied by a message stating, “The waiting period has expired. Compromised data can be downloaded from the leak page.”
This statement suggests that negotiations between the ransomware group and the attorney general’s office have reached a deadlock, with the latter refusing to meet the ransom demands. Cloak has released images alleged to be documents stolen from the attorney general’s systems to substantiate their claims.
However, the Virginia attorney general’s office has yet to officially acknowledge or confirm Cloak’s claims. At this stage, critical details remain undisclosed, including whether a ransom was paid, the amount demanded by Cloak, the nature and extent of the compromised data, and the specific methods used by the attackers to breach the attorney general’s network. We are also awaiting the official response from the attorney general’s office regarding the latest development.
For your information, Cloak is a ransomware group that emerged in 2022 and gained prominence in 2023. The group mainly targets small to medium-sized businesses in Europe and Asia, particularly Germany. It also employs malware designed to both exfiltrate data and encrypt computer systems, thereby compelling victims to pay a ransom.
Victims who refuse to pay face their stolen data published on Cloak’s data leak site for free download. The group’s payment rate is surprisingly high at 91-96%, showing how effectively it forces its victims.
Since its emergence, Cloak has claimed responsibility for 13 confirmed ransomware attacks, including attacks on the Canadian town of Ponoka and the German municipality of Gemeinde Kaisersbach in 2024, and 54 unconfirmed attacks (where targeted organizations did not acknowledge the intrusions). The attack on the Virginia attorney general marks Cloak’s first confirmed operation in 2025.
Top/Featured Image via Consumer Financial Services Law Monitor