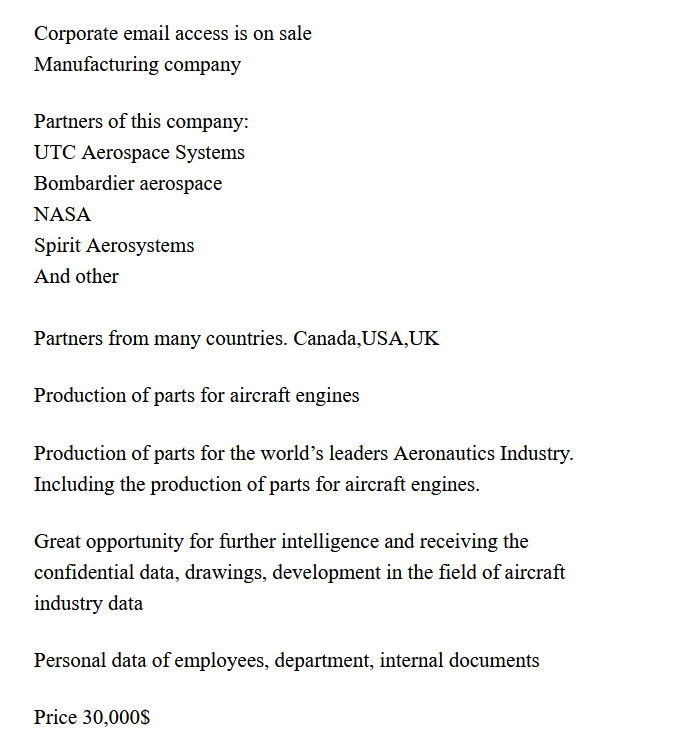
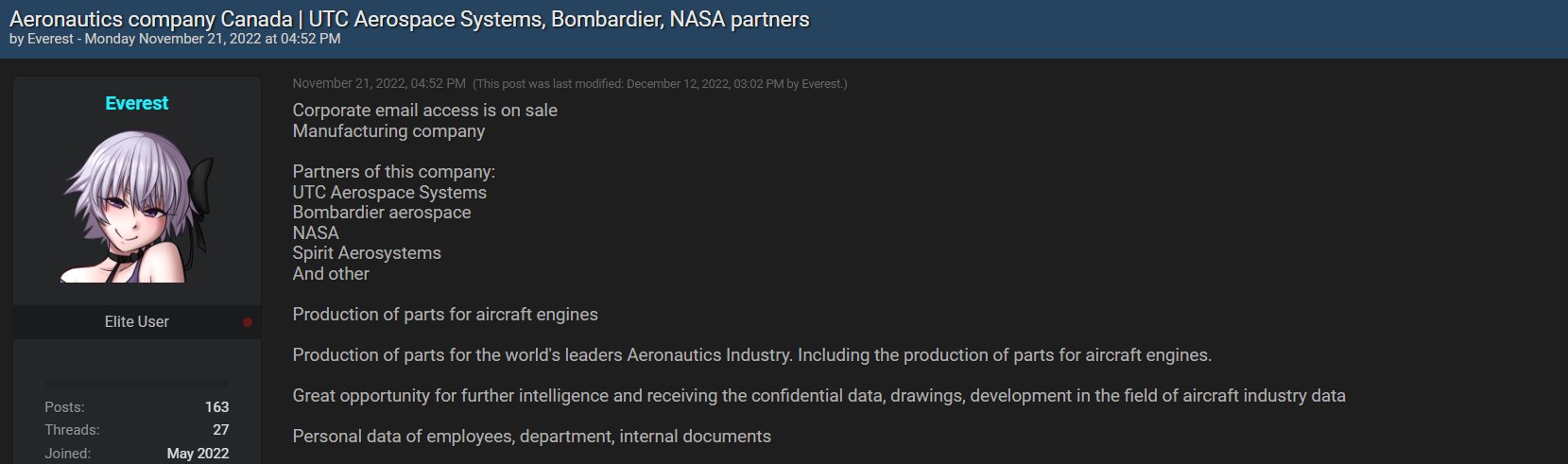
Everest ransomware group claimed that they are in possession of sensitive system data from aeronautics companies, including NASA. Based on the reports so far, it could be ascertained that the ransomware group has not made any payment demands to the victims yet. However, they have put a price of $30,000 for whoever wants to buy the sensitive data from their leak site.
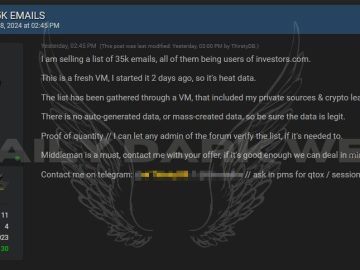
According to the group’s leak site, they have confidential data, including corporate email access that, they claimed, to be a “great opportunity for further intelligence.”
Technology security company FalconFeedsio tweeted about the ransomware group uploading data from aerospace organizations on their leak site.

The post claimed to have data belonging to countries including Canada, the United States of America, and the United Kingdom. Going by the claims of the Everest group, the aerospace industry may have to work promptly to wipe out the data before it reaches adversaries. The group also tried to create a sense of urgency and fear by hinting at who might benefit from acquiring trade secrets.
Seeing the data is up for sale on the leak site it could be inferred that the gang has no hope of finding a favorable response, much like the Play ransomware group that allegedly put exfiltrated data from the car company Volvo on the hacker forum this week.
Hackers are increasingly turning to sell sensitive stolen data on their leak sites as several government agencies have discouraged companies from paying a ransom following an attack.

Modus operandi of the Everest ransomware group
According to a report by NCC Group, the Everest ransomware group had earlier offered access to the IT infrastructure of its victim’s systems for a fee if their ransom demands were not met. The Russian-speaking threat actor group Everest has also targeted several government offices of states, including Argentina, Peru, and Brazil.
Digital Recovery, a data recovery company, reported that the ransomware was discovered in 2018, and is a part of the Everbe 2.0 ransomware family. It is made using Embrace, Hyena Locker PainLocker, and EvilLocker ransomware.
The group, which is named after its ransomware, goes for double extortion as a maneuver to increase profit by seeking double ransom. One for the decryption key and the other payment for not leaking the encrypted data.
To be watchful of ransomware crawling into the systems, it is very important not to entertain suspicious emails that may be phishing attacks by cybercriminals. It can appear as spammy emails, commercial emails, advertising emails, or emails offering financial information. Such emails often carry malicious word or excel attachments. This is one of the main modes of reaching the target used by the Everest ransomware group.
Moreover, the Everest group was observed to be moving laterally across networks upon breaching the systems using compromised user accounts of victims. They have also used remote desktop protocol to move laterally. Researchers and solutions providers do have the necessary tools to recover ransomware extensions provided they are called sooner than later.