GitHub has introduced a new option to set up code scanning for a repository known as “default setup,” designed to help developers configure it automatically with just a few clicks.
While the CodeQL code analysis engine, which powers GitHub’s code scanning, comes with support for many languages and compilers, the new option only shows up for Python, JavaScript, and Ruby repositories.
Product marketing manager Walker Chabbott said that GitHub is working on expanding support to more languages over the next six months.
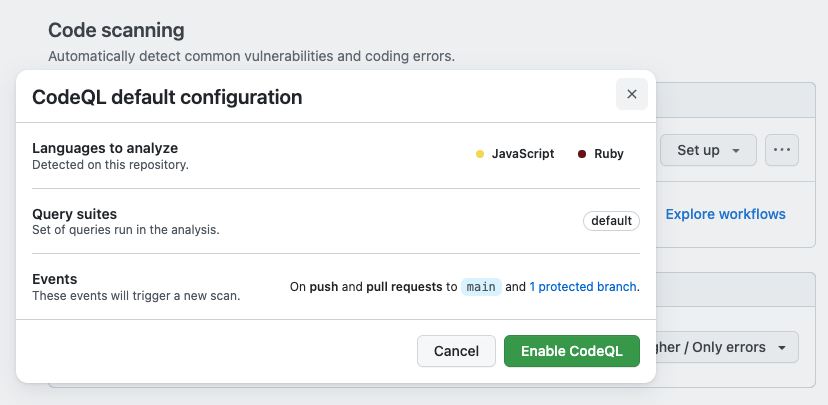
To use the new code scanning setup option, you have to go to “Code security and analysis” in your repo’s settings, click the “Set up” drop-down menu, and choose the Default option.
“When you click on ‘Default,’ you’ll automatically see a tailored configuration summary based on the contents of the repository,” Chabbott said.
“This includes the languages detected in the repository, the query packs that will be used, and the events that will trigger scans. In the future, these options will be customizable.”
After you hit “Enable CodeQL,” code scanning will immediately start looking for vulnerabilities in the repo to help you patch the flaws it finds and create more secure software.
The CodeQL code analysis engine was added to the GitHub platform’s capabilities after the Semmle code-analysis platform was acquired in September 2019.
The first code scanning beta at GitHub Satellite in May 2020, and its general availability was announced four months later, in September 2020.
During beta testing, the feature was used to scan over 12,000 repositories 1.4 million times to find more than 20,000 security issues, including remote code execution (RCE), SQL injection, and cross-site scripting (XSS) flaws.
Code scanning is free for all public repositories, and it’s also available as a GitHub Advanced Security feature for GitHub Enterprise private repositories.
Last month, GitHub also rolled out support for the free scanning of exposed secrets (such as auth tokens and credentials) to all public repositories.







