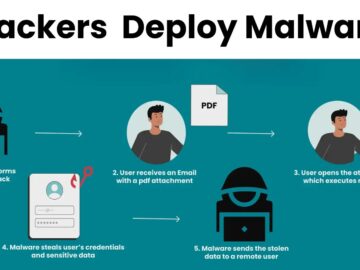
Hackers are leveraging a sophisticated social engineering technique dubbed “ClickFix” to trick Windows users into executing malicious scripts on their systems.
This method capitalizes on fake error pages and notifications that mimic legitimate alerts, often resembling Chrome browser errors or system warnings.
These deceptive pop-ups prompt users to “fix” an alleged issue by copying and running a hidden PowerShell script, ultimately leading to malware infection.
Cybersecurity experts warn that this technique is particularly dangerous due to its reliance on user interaction, bypassing traditional security measures like firewalls or antivirus software.
According to Kaspersky Report, the ClickFix attack typically begins with a convincing pretext, such as a pop-up claiming a webpage cannot load, a document is inaccessible, or a browser update is required.

In some cases, attackers host fraudulent websites or compromise legitimate ones to display these alerts, while others distribute instructions via email, social media, or messaging apps.
Fake CAPTCHAs to Browser Updates
Variations of the scam include fake CAPTCHAs asking users to “prove they’re not robots” by running a script, or fabricated issues with microphones and cameras during supposed Zoom or Google Meet calls.

The instructions are deceptively simple: copy a provided code (often hidden from view), open the Windows Run dialog with [Win] + [R], paste the script using [Ctrl] + [V], and execute it by pressing [Enter].
Unbeknownst to the victim, this sequence downloads and installs malware, ranging from ransomware to spyware, depending on the campaign.
Notably, Windows 11 users face an additional risk, as attackers can guide them to execute scripts via the system search bar, expanding the attack surface beyond the traditional Run dialog.
The implications of ClickFix are severe, as it transforms the user into an unwitting accomplice in their own system’s compromise.
Protective strategies must go beyond technical safeguards like blocking the [Win] + [R] shortcut, which is not foolproof given alternative execution methods.
Experts emphasize the critical need for employee training to recognize suspicious prompts for manual system changes, a telltale sign of malice.
As attackers refine their pretexts-from browser refresh errors to urgent plugin installations-vigilance remains the first line of defense against these insidious social engineering ploys.
Organizations and individuals alike are urged to stay informed about such tactics and foster a culture of skepticism toward unsolicited system instructions, ensuring that a momentary lapse in judgment does not lead to a catastrophic breach.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!