How to Hunt for Zip Slip Exploits in Open Source Bug Bounty | huntr.dev #methodology

Source link
Related Articles
All Mix →The importance of incorporate web application scanning for a complete EASM solution
Table of Contents What is web application scanning? What is EASM? Why do the best EASM solutions naturally incorporate application scanning capabilities? How Detectify’s Surface…
Advanced Workflows with Inbox Views
By default, HackerOne offers a standard vulnerability disclosure workflow that supports most security teams out there. But one size doesn’t fit all. We all like…
[tl;dr sec] #170 – Prototype Pollution, Fuzzing, SOC Metrics
Table of Contents Focusing on the Right Stuff 📢 Drata’s Compliance Trends Report 2023 📜 In this newsletter… Web Security 📢 We Hack Purple –…
Don’t Anticipate Greatness | Daniel Miessler
Anticipation of greatness is a near guarantee of mediocrity. It sucks to have to psyche yourself out, but it helps to do so if you…
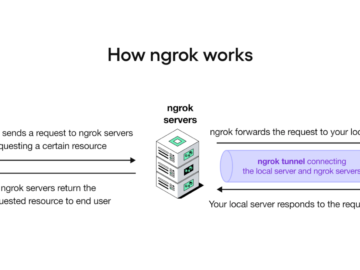
Using ngrok to proxy internal servers in restrictive environments
When gaining shell access to a machine on a network, a promising attack vector is to check the internal network for web applications and services…
Alex Rice and Zane Lackey Discuss Modern Security for Practitioners
Our co-founder and CTO, Alex Rice, was a recent guest on The Modern Security Series by Signal Sciences, along with Signal Sciences’ co-founder and CSO,…